Vishing and SSO abuse are accelerating rapid SaaS extortion
Summarize with:
Share
Vishing and SSO abuse are accelerating rapid SaaS extortion
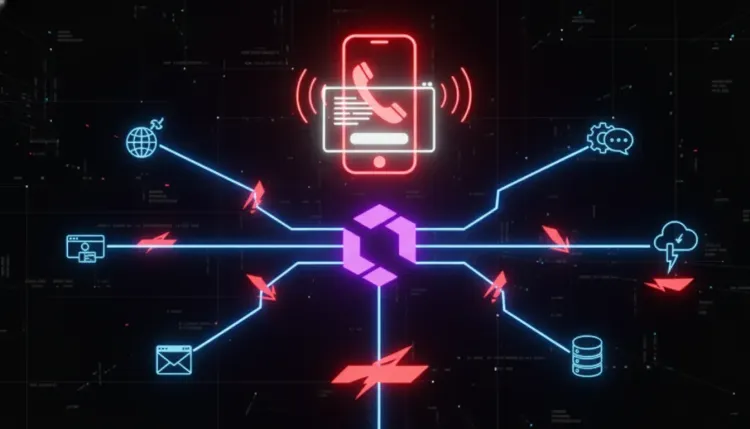
The most dangerous part of modern SaaS intrusions is not always malware. Sometimes it is speed, trust, and identity. New reporting on activity tracked as Cordial Spider and Snarky Spider shows how cybercrime groups can use vishing, adversary-in-the-middle login pages, and identity-provider abuse to move from a single phone call to broad SaaS compromise in less than an hour.
That should worry defenders because the attack path stays inside tools many organizations already trust. Once attackers capture credentials and multi-factor authentication codes, they can pivot through the identity provider and move laterally across connected SaaS applications with very little endpoint noise. This is a cloud-era social engineering problem, but it is equally an identity and access management problem.
Why this campaign matters
According to recent reporting and vendor threat intelligence, these groups operate almost entirely within SaaS environments, minimizing forensic footprint while maximizing time-to-impact. Instead of deploying a heavy malware chain first, they focus on trusted workflows:
- impersonating internal IT or help-desk staff over voice calls
- directing users to fake SSO login pages
- capturing credentials and MFA codes in real time
- enrolling new devices and removing existing ones to preserve access
- suppressing warning emails by creating inbox rules
- pivoting from the identity provider into business-critical SaaS platforms
That sequence is exactly why these intrusions are hard to catch early. Each step abuses routine enterprise behavior rather than obviously malicious binaries.
How the intrusion chain works
1. Voice pretext creates trust
Attackers call users while pretending to be support or internal IT staff. The goal is not only to steal a password. It is to create urgency and lower skepticism long enough to get the victim into an attacker-controlled login flow.
2. AiTM pages capture the full session path
Victims are sent to malicious SSO-themed pages that proxy the real authentication experience. This lets the threat actor collect credentials and intercept MFA challenges in the same interaction.
3. The identity provider becomes the pivot point
Once inside the IdP, the attacker can use established trust relationships to reach multiple connected applications. That means a single compromise can expose Google Workspace, SharePoint, Salesforce, HubSpot, and other SaaS services without separately exploiting each one.
4. Attackers suppress the obvious alerts
Threat reporting says the groups often register a new device, remove existing trusted devices, and create inbox rules to delete automated email notifications about those changes. That strips away some of the defender's easiest early-warning signals.
5. Data theft and extortion follow quickly
After obtaining broader access, the operators look for high-value files, reports, and business data that can support extortion. In this model, data breach impact can arrive long before defenders see traditional malware indicators.
Why SaaS-only intrusion paths are so effective
Minimal endpoint evidence
If the attacker spends most of the campaign inside browsers, SaaS sessions, and native administrative features, endpoint telemetry may show far less than defenders expect during a major intrusion.
One login can unlock many services
This is the strategic weakness of over-trusted federated identity. The convenience of SSO becomes an attack amplifier when a compromised session can reach dozens of downstream services.
Notification controls can be turned against the victim
If adversaries can delete or hide registration alerts, the organization may lose precious time before the incident is discovered.
What defenders should do now
Harden identity workflows, not just endpoints
- Require phishing-resistant MFA where possible.
- Review device-registration controls and approval workflows.
- Tighten conditional access around new device enrollment, impossible travel, and unfamiliar sign-in patterns.
Treat help-desk impersonation as a top-tier control gap
- Train staff to treat unsolicited support calls as high risk.
- Use out-of-band verification for password resets, MFA resets, and new-device approvals.
- Build scripts and policies so real IT staff never need users to read MFA codes back over the phone.
Hunt for quiet SaaS abuse
- Review inbox rules that delete security notifications.
- Look for suspicious device enrollment, rapid privilege escalation, and unusual access across multiple SaaS applications from a single identity.
- Focus on identity telemetry, audit trails, and administrator changes, not just malware detections.
Reduce blast radius inside the SaaS estate
- Limit standing privileges.
- Segment administrative roles across SaaS platforms.
- Review which applications are federated to the main IdP and whether all of them truly need broad user access.
Strategic takeaway
Rapid SaaS extortion campaigns work because many organizations still treat identity compromise like a single-account issue instead of an environment-wide trust failure. When one stolen session can unlock multiple cloud services, hide alerts, and expose sensitive business data, the old boundary between phishing and full compromise disappears.
The practical lesson is simple: if your users can be talked into a fake SSO flow, your SaaS estate may already be one phone call away from a cross-platform intrusion. Defenders need to instrument identity, harden support workflows, and respond to suspicious sign-in changes with the urgency of a live breach.
Why are these campaigns harder to detect than traditional intrusions?
Because much of the attacker activity happens inside legitimate SaaS services and trusted login flows. That reduces obvious endpoint artifacts and can make the intrusion look like normal user behavior at first.
What makes SSO abuse so dangerous?
A single identity-provider compromise can grant access to many connected applications. That gives attackers an efficient path to lateral movement, data theft, and extortion without needing separate exploits for each SaaS platform.
What is the first control to review?
Start with MFA reset flows, device enrollment approvals, and monitoring for unusual identity-provider activity. If those are weak, the rest of the SaaS stack is easier to abuse.
References
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Cloud & Application Security → Cloud & Application Security
Cloud & Application SecurityLiteLLM SQL injection flaw puts AI gateways on the front line
LiteLLM SQL injection flaw puts AI gateways on the front line CVE-2026-42208 matters because it turns an AI gateway into a high-value choke point for attackers....
 Cloud & Application Security
Cloud & Application SecurityConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk ConsentFix v3 matters because it shifts Azure account compromise away from password th...
 Cloud & Application Security
Cloud & Application SecurityPyTorch Lightning supply-chain compromise puts AI developer credentials at risk
PyTorch Lightning supply-chain compromise puts AI developer credentials at risk The most dangerous supply-chain incidents are not always the ones that hit opera...