LiteLLM SQL injection flaw puts AI gateways on the front line
Summarize with:

Share
LiteLLM SQL injection flaw puts AI gateways on the front line
CVE-2026-42208 matters because it turns an AI gateway into a high-value choke point for attackers. LiteLLM is widely used as a proxy layer in front of multiple LLM providers, so an unauthenticated SQL injection bug in that proxy is not just a bug in a niche tool. It is a risk to the credentials, routing logic, and trust boundaries that sit between users, applications, and upstream model providers.
CISA has already added the flaw to its Known Exploited Vulnerabilities catalog. That should change the priority immediately. When a weakness on an AI proxy is already being exploited, defenders should treat it as a live vulnerability management issue rather than a routine backlog item.
What happened
According to the GitHub security advisory for LiteLLM, the vulnerable code path mixed a caller-supplied API key value into a database query used during proxy key verification instead of passing it safely as a parameter. The advisory says an unauthenticated attacker could send a crafted Authorization header to an LLM API route such as POST /chat/completions and reach the vulnerable query through an error-handling path.
That detail is important because it shifts the story from "edge case bug" to realistic external exposure. If LiteLLM is reachable from user-facing applications, internal developer tools, or shared AI platforms, the proxy itself becomes part of the attack surface.
Why AI gateways deserve more defensive attention
LiteLLM is not only forwarding prompts. In many environments it also centralizes provider credentials, team keys, usage controls, model routing, and operational telemetry. That makes the proxy a concentration point for both cost governance and sensitive access.
An exploited SQL injection flaw in that layer can create several problems at once:
- exposure of database-stored proxy information
- potential access to credentials managed by the platform
- abuse of trusted internal AI workflows
- easier follow-on lateral movement into surrounding application or cloud services
This is why AI infrastructure should now be treated more like other security-critical middleware. If the gateway is compromised, the attacker may inherit visibility into how teams consume models, which integrations exist, and where privileged tokens are stored.
The enterprise risk is bigger than prompt security
A lot of AI security discussion still centers on model misuse, prompt injection, or data leakage through completions. Those are real concerns, but CVE-2026-42208 is a reminder that ordinary application-security failures still apply to AI stacks.
In practice, this means defenders need to examine AI gateways with the same rigor they apply to internet-facing admin panels, API brokers, or secrets-adjacent middleware. If an attacker can read or potentially modify the proxy database, the blast radius may include service configuration, authentication paths, and the credentials used to broker access to external AI services.
That creates both immediate containment work and a likely incident response burden. Even after patching, teams may need to review whether stored provider keys, internal team tokens, or other proxy-managed secrets should be rotated.
What defenders should do now
1. Upgrade or apply the vendor workaround immediately
The LiteLLM advisory says the issue is fixed in version 1.83.7 and later. If an immediate upgrade is not possible, the vendor's documented workaround is to set disable_error_logs: true under general_settings to remove the vulnerable unauthenticated path.
2. Treat internet exposure as a priority finding
Identify every LiteLLM instance exposed to the internet, partner environments, or semi-trusted application traffic. AI gateways often get deployed quickly for product experiments and internal platform work, so do not assume asset inventories are complete.
3. Review stored secrets and trust relationships
Because the proxy may manage upstream provider credentials and team-level keys, patching alone may not be enough. Review whether tokens, API keys, or other secrets stored behind the proxy should be rotated, especially if exposure existed before remediation.
4. Hunt around the proxy, not just on the proxy
Look for suspicious requests to LLM API routes, unusual error-path activity, unexpected database access patterns, and anomalies in downstream model usage. Also review adjacent systems that relied on the proxy for access control, billing governance, or provider selection.
5. Reclassify AI gateways as critical middleware
This is the broader lesson. AI proxies should be included in regular security review scopes, patch SLAs, secret-rotation playbooks, and architecture threat models. If the organization depends on them to broker production access to multiple model providers, they deserve the same protection level as other sensitive API infrastructure.
Strategic takeaway
CVE-2026-42208 is a useful wake-up call for defenders building AI-enabled products and internal AI platforms. The security problem is not only what the model does with data. It is also what the surrounding control plane can expose when ordinary web-application weaknesses hit a central AI gateway.
Organizations that have embraced AI quickly should use this flaw as a prompt to audit proxy exposure, key storage, patch speed, and ownership. The teams that treat AI gateways like critical infrastructure will be in a much better position than the ones treating them like disposable developer tooling.
Is this flaw remotely exploitable?
Yes. The advisory describes an unauthenticated attacker reaching the vulnerable query by sending a crafted Authorization header to LiteLLM API routes.
Why does an AI proxy issue matter so much?
Because AI gateways often sit in front of multiple upstream providers and can manage credentials, routing, and policy. A compromise there can expose more than a single application component.
What is the first practical action for defenders?
Upgrade LiteLLM to 1.83.7 or later, or apply the vendor workaround immediately if upgrade timing is constrained.
References
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Cloud & Application Security →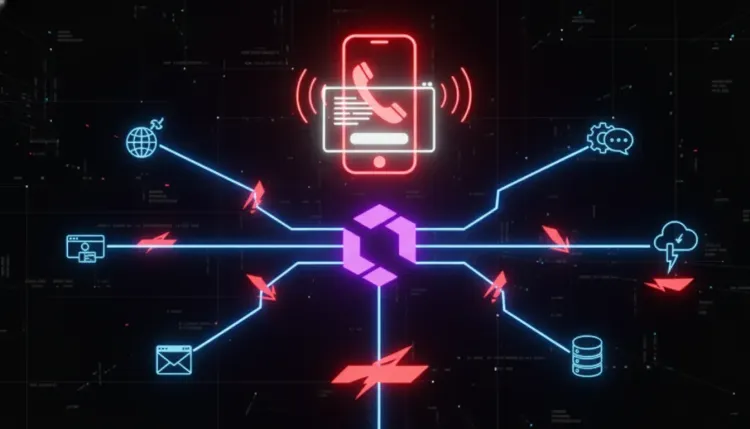 Cloud & Application Security
Cloud & Application SecurityVishing and SSO abuse are accelerating rapid SaaS extortion
Vishing and SSO abuse are accelerating rapid SaaS extortion The most dangerous part of modern SaaS intrusions is not always malware. Sometimes it is speed, trus...
 Cloud & Application Security
Cloud & Application SecurityConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk ConsentFix v3 matters because it shifts Azure account compromise away from password th...
 Cloud & Application Security
Cloud & Application SecurityPyTorch Lightning supply-chain compromise puts AI developer credentials at risk
PyTorch Lightning supply-chain compromise puts AI developer credentials at risk The most dangerous supply-chain incidents are not always the ones that hit opera...