ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk
Summarize with:

Share
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk
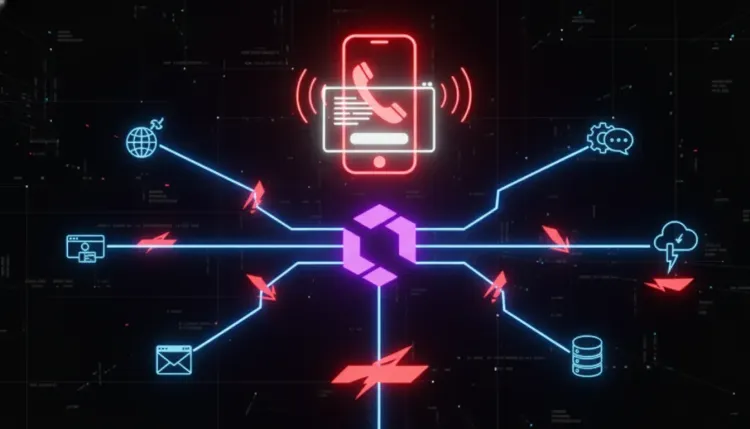
ConsentFix v3 matters because it shifts Azure account compromise away from password theft and toward token capture and automation. Public reporting says the technique abuses a legitimate Microsoft OAuth flow, tricks users into handing over an authorization-code redirect, and then exchanges that code for tokens almost immediately through automated infrastructure.
That changes the defensive conversation. Many organizations still frame phishing around credential harvesting or malware delivery. ConsentFix v3 shows how social engineering can instead weaponize normal cloud trust paths, making the user interaction look closer to a legitimate sign-in than a traditional fake login page.
What ConsentFix v3 appears to do
According to BleepingComputer's reporting on research from Push Security, attackers first identify whether a target organization uses Microsoft Azure or Microsoft 365. They then gather employee details for tailored lures, build phishing infrastructure across commodity services, and guide victims through a real Microsoft login flow.
The key step is what happens next. Instead of stealing a password directly, the victim is manipulated into copying or dragging a localhost redirect URL containing an OAuth authorization code back into attacker-controlled infrastructure. That code is then sent to an automation pipeline, which exchanges it for tokens in near real time.
In practice, that means the attacker is not trying to break Microsoft authentication. The attacker is trying to abuse it. If the flow succeeds, the value is in the tokens and the access they enable across email, files, and connected cloud services.
Why this is more dangerous than a basic phishing story
1. It exploits trusted application behavior
Microsoft's own Entra guidance makes clear that user and admin consent settings are a core part of cloud access governance. ConsentFix v3 is concerning because it rides on top of legitimate OAuth behavior instead of obviously malicious binaries or fake password prompts.
2. MFA is not the same as safety from token abuse
This is the practical lesson defenders should keep in mind. If a user completes a legitimate sign-in and the attacker captures the authorization outcome, the security discussion moves beyond passwords. Organizations that treat MFA as the end of the control story can miss how token-based abuse changes the attack surface.
3. Automation makes the technique more scalable
The reported use of platforms such as Pipedream for code capture and token exchange suggests a repeatable playbook, not a one-off trick. Once collection, exchange, and handoff are automated, attackers can run higher-volume campaigns with less manual effort.
What Microsoft guidance adds to the story
Microsoft's Entra documentation recommends restricting user consent and allowing consent only for applications from verified publishers where possible. That guidance matters here because OAuth abuse often becomes easier when tenants allow broad or poorly understood consent behavior.
Microsoft also distinguishes between user-consent and admin-consent scenarios, which is operationally important. Even where a specific campaign uses pre-trusted first-party applications rather than a brand-new rogue app, the larger lesson still holds: cloud administrators need tighter visibility into what flows are being authorized, by whom, and under what policy.
What defenders should do now
🔴 Tighten consent and application governance
- Review Microsoft Entra user-consent settings across the tenant.
- Prefer stricter policies that limit consent to verified publishers and low-risk permissions where business requirements allow.
- Audit which applications are broadly trusted and whether that trust is still justified.
🔴 Hunt for suspicious token and consent activity
- Monitor for unusual sign-ins followed by rapid access to mailbox or file data.
- Correlate suspicious user interactions with new token issuance, consent events, and abnormal cloud application access.
- Feed cloud-identity telemetry into incident response playbooks, not just email-security dashboards.
🟠 Reduce user exposure to interactive phishing flows
- Update awareness training so users understand that a real Microsoft login prompt can still be part of an attack.
- Warn users never to paste redirect URLs, localhost callback strings, or authorization responses into websites, chat tools, or forms.
- Add browser and email detections for lures that push users into unusual copy-paste or drag-and-drop authentication steps.
🟠 Focus on identity resilience, not just credential hygiene
- Make identity and access management reviews part of routine security operations.
- Revisit conditional access, device binding, and app restrictions for privileged and high-value users.
- Ensure cloud containment steps include session and token revocation, not only password resets.
Strategic takeaway
ConsentFix v3 is a strong reminder that identity attacks are increasingly about abusing trusted workflows rather than defeating them outright. For defenders, the real question is no longer only "Can we stop fake logins?" It is also "Can we detect and contain legitimate-looking authorization flows that end in attacker-controlled tokens?"
That is a harder problem, but it is the one cloud security teams need to get better at now.
Does ConsentFix v3 steal passwords?
Not necessarily. The reported technique focuses on capturing OAuth authorization outcomes and exchanging them for tokens, which can be enough to access cloud resources without traditional password theft.
Why is this different from a normal Microsoft phishing page?
Because the flow reportedly relies on legitimate Microsoft authentication steps and then manipulates the victim into handing over the redirect data that completes the authorization process.
What is the first practical control to review?
Start with Microsoft Entra consent settings, application trust posture, and your ability to revoke active sessions and tokens quickly during an investigation.
References
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Cloud & Application Security → Cloud & Application Security
Cloud & Application SecurityLiteLLM SQL injection flaw puts AI gateways on the front line
LiteLLM SQL injection flaw puts AI gateways on the front line CVE-2026-42208 matters because it turns an AI gateway into a high-value choke point for attackers....
 Cloud & Application Security
Cloud & Application SecurityVishing and SSO abuse are accelerating rapid SaaS extortion
Vishing and SSO abuse are accelerating rapid SaaS extortion The most dangerous part of modern SaaS intrusions is not always malware. Sometimes it is speed, trus...
 Cloud & Application Security
Cloud & Application SecurityPyTorch Lightning supply-chain compromise puts AI developer credentials at risk
PyTorch Lightning supply-chain compromise puts AI developer credentials at risk The most dangerous supply-chain incidents are not always the ones that hit opera...