Iranian PLC Attacks Disrupt U.S. Critical Infrastructure
Summarize with:

Share
Iranian PLC Attacks Disrupt U.S. Critical Infrastructure
Executive Summary
Iranian-affiliated advanced persistent threat actors have been targeting internet-exposed PLCs across U.S. critical infrastructure since at least March 2026, according to a joint advisory published by CISA, the FBI, NSA, EPA, DOE, and U.S. Cyber Command on April 7. The agencies say the activity has already caused disruptions in government services, water and wastewater, and energy environments through malicious manipulation of project files and HMI or SCADA displays, with some victims reporting operational disruption and financial loss.
For defenders, the key point is simple: this is not a theoretical OT warning. It is an active campaign aimed at exposed control systems and engineering access paths. Any organization with reachable PLCs, insecure remote maintenance, or weak OT firewall boundaries should treat this as an urgent exposure review and incident response problem.
What happened?
- April 7, 2026: CISA and partner agencies published advisory AA26-097A warning of active exploitation targeting internet-facing operational technology devices, including Rockwell Automation and Allen-Bradley PLCs.
- The advisory says the campaign has been ongoing since at least March 2026.
- Affected sectors called out by the agencies include government services, water and wastewater systems, and energy.
- Reported attacker behavior includes modifying PLC project files and manipulating data shown on HMI and SCADA systems.
- The agencies say some victim organizations experienced operational disruption and financial loss.
- The advisory attributes the activity to Iranian-affiliated APT actors and notes similarities to earlier CyberAv3ngers-linked PLC disruption campaigns.
- The agencies also warn that targeting of ports tied to other OT protocols suggests additional PLC brands may also be at risk, not only Rockwell devices.
Who is affected?
The most directly exposed organizations are operators with internet-reachable PLCs or poorly controlled remote access into OT environments. Based on the advisory, the highest-risk environments currently include:
- local governments and municipal operations
- water and wastewater facilities
- energy operators
- industrial sites using Rockwell Automation or Allen-Bradley PLCs
- organizations with engineering workstations or vendor tooling that can reach control systems from untrusted networks
The agencies specifically mention CompactLogix and Micro850 targets, but defenders should not read that as a safe list for every other OT estate. If remote administration, programming access, cellular connectivity, or third-party maintenance paths exist, the broader attack surface is likely bigger than teams expect.
Initial access and kill chain
The current picture is operationally important because the attackers do not appear to need a noisy enterprise IT foothold first. According to the advisory, the actors used overseas-hosted infrastructure and configuration software, including Rockwell Automation's Studio 5000 Logix Designer, to establish accepted connections to exposed PLCs.
A likely attack flow looks like this:
- Identify internet-exposed PLCs or related remote access paths.
- Reach the device over ports associated with OT protocols or remote administration.
- Use engineering or management connectivity to interact with PLC project files.
- Manipulate logic or displayed data on HMI and SCADA systems.
- In some cases, deploy remote access tooling such as Dropbear SSH to maintain control.
- Cause disruption, process integrity loss, or downstream financial impact.
MITRE-aligned view
- Initial Access: Internet-accessible OT devices and exposed remote access paths
- Execution: Malicious interaction with PLC project files and controller logic
- Persistence / Remote Access: Dropbear SSH on victim endpoints
- Command and Control: Remote connectivity from leased overseas infrastructure, potentially establishing ongoing command-and-control channels
- Impact: Process disruption, manipulated displays, operational outages, and business loss
Indicators and detection
Defenders should prioritize visibility around direct access into OT devices, especially from unexpected geographies, third-party hosting providers, or unusual engineering workflows.
Focus on:
- inbound traffic to OT-related ports including 44818, 2222, 102, 22, and 502
- access to PLCs from cloud-hosted or overseas IP space
- unexpected use of engineering software against internet-facing devices
- suspicious changes to controller logic, project files, or HMI display values
- installation or execution of Dropbear SSH or similar remote access tools on OT-adjacent systems
- remote sessions occurring outside approved maintenance windows
Example Splunk hunt
splindex=firewall OR index=netflow OR index=ids (dest_port=44818 OR dest_port=2222 OR dest_port=102 OR dest_port=22 OR dest_port=502) | stats count min(_time) as firstSeen max(_time) as lastSeen values(src_ip) as src_ip values(dest_ip) as dest_ip values(dest_port) as ports by src_country, action | where src_country!="US"
This is an example pattern, not a complete detection. OT teams should also review engineering workstation logs, controller configuration change records, remote access logs, and plant-floor change approvals.
Containment and remediation checklist
🔴 Immediate containment (0-24h)
- Identify every PLC or OT gateway reachable from the internet.
- Remove direct internet exposure wherever possible.
- Route remote access through secure, monitored gateways only.
- Review firewall rules for exposed ports 44818, 2222, 102, 22, and 502.
- Check for unauthorized project file changes, logic changes, or anomalous HMI display behavior.
- Hunt for Dropbear SSH or unapproved remote access software on OT-adjacent systems.
- Validate whether cellular modems or unmanaged maintenance paths exist.
- Preserve logs before making large containment changes.
- Escalate into formal OT incident response if any suspicious controller interaction is found.
🟠 Hardening (24-72h)
- Enforce strong network segmentation between enterprise IT and control networks.
- Restrict engineering workstation access to named administrators and approved jump paths.
- Validate multifactor authentication for remote support and vendor access.
- Disable unused services, stale accounts, and default credentials.
- Review controller mode settings and physical protections against unauthorized modification.
- Confirm offline backups exist for controller logic, configurations, and recovery images.
- Baseline normal PLC communication patterns to improve detection.
- Review vendor guidance for hardening Rockwell and other OT assets.
🟡 Longer-term controls (1-4 weeks)
- Build routine exposure management for OT and remote maintenance paths.
- Add passive OT monitoring where direct endpoint tooling is not feasible.
- Exercise plant-specific response playbooks for controller integrity loss.
- Align engineering change control with cybersecurity review.
- Reassess third-party maintenance trust and logging requirements.
- Integrate OT telemetry into broader threat intelligence and detection workflows.
- Test recovery procedures that assume manipulated logic, not just device outage.
Strategic analysis
This advisory matters because it shows adversaries are willing to move from access into direct operational effect. That changes the framing from ordinary espionage or opportunistic scanning to disruption-oriented OT activity.
The agencies' reporting also highlights a recurring truth in industrial environments: attackers often do not need a sophisticated zero-day if exposed control paths already exist. Weak perimeter controls, unmanaged vendor access, and poorly separated engineering workflows can be enough.
For defenders, the lesson is broader than this specific Iranian campaign. OT resilience now depends on reducing exposure, validating remote access paths, and treating controller integrity as a frontline security issue, not a niche plant-floor problem.
What happened?
U.S. agencies warned that Iranian-affiliated actors are actively targeting internet-exposed PLCs across multiple critical infrastructure sectors and have already caused operational disruption in some cases.
Who is most at risk?
Operators in water, wastewater, energy, local government, and other industrial environments with exposed PLCs or weak remote maintenance controls face the highest risk.
Which products are mentioned in the advisory?
The agencies specifically call out Rockwell Automation and Allen-Bradley PLCs, including CompactLogix and Micro850 devices, while warning that other vendors may also be in scope.
How are the attackers getting in?
The advisory says the actors used overseas-hosted infrastructure and configuration software to reach internet-facing PLCs and establish accepted connections for malicious interaction.
What should defenders do first?
Find and remove direct internet exposure, review OT-related inbound traffic and controller changes, and begin OT incident response if suspicious activity is found.
Is this only a U.S. problem?
The advisory focuses on U.S. victims, but the underlying lesson applies more broadly. Any organization with exposed PLCs or insecure OT remote access should review risk immediately.
References
- CISA Advisory AA26-097A: Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
- Industrial Cyber: Ongoing cyberattacks targeting internet-connected PLCs disrupt US critical infrastructure, agencies warn
- The Register: Iran intruders disrupting US water, energy facilities
- Politico: Iranian hackers are targeting US energy and water sectors, federal agencies warn
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Threat Hunting & Intel →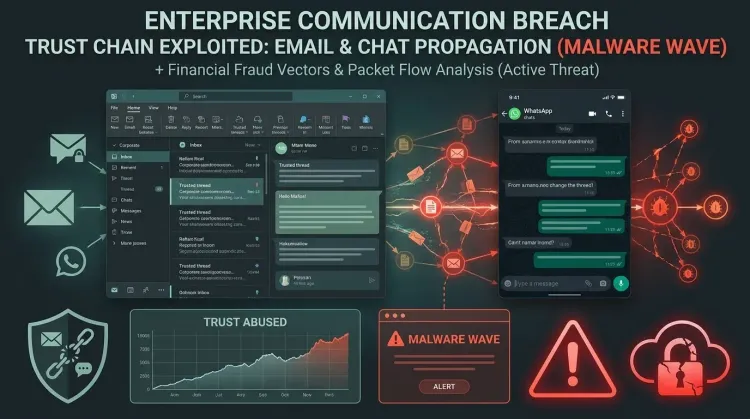 Threat Hunting & Intel
Threat Hunting & IntelTCLBANKER turns WhatsApp and Outlook into trusted malware delivery channels
TCLBANKER turns WhatsApp and Outlook into trusted malware delivery channels The most important detail in Elastic's new TCLBANKER research is not just that a Bra...
 Threat Hunting & Intel
Threat Hunting & IntelDAEMON Tools supply-chain attack turns trusted installers into a malware delivery path
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path The most important part of the DAEMON Tools incident is not that malware...
 Threat Hunting & Intel
Threat Hunting & IntelCVE-2026-41940 turns exposed cPanel and WHM servers into control-plane takeover targets
CVE-2026-41940 turns exposed cPanel and WHM servers into control-plane takeover targets CVE-2026-41940 is a critical authentication bypass in cPanel and WHM, an...