APT28 BeardShell Campaign Targets Ukraine | 2026
Summarize with:

Share
APT28: BeardShell and Covenant Hit Ukraine | 2026
Executive Summary
On March 11, 2026, ESET detailed how APT28 (aka Sednit/Fancy Bear) has reactivated a more advanced malware pipeline centered on BeardShell, SlimAgent, and a heavily modified Covenant framework to sustain espionage against Ukrainian military personnel and related government targets. The campaign has been active since April 2024, with researchers observing continued deployment through 2025 and 2026.
For defenders, the story matters because it combines a modernized advanced persistent threat toolkit with resilient cloud-based command-and-control channels, deterministic host identifiers, and fallback implants designed to survive infrastructure disruption. In practice, this raises the bar for hunting, especially in environments where cloud storage traffic blends into normal operations.
What happened?
- April 2024: CERT-UA discovered SlimAgent on a Ukrainian government machine.
- 2024 onward: ESET linked SlimAgent to historical XAgent code lineage used by APT28.
- 2024-2026: Researchers observed BeardShell in long-term surveillance operations focused on Ukrainian military personnel.
- Since July 2025: APT28's modified Covenant framework reportedly shifted to the Filen cloud provider for C2; earlier variants used pCloud and Koofr.
- March 2026: ESET publicly assessed that APT28's advanced malware development team has effectively returned to active operations.
- Reported / contextual link: Recent APT28 activity also included exploitation of Microsoft Office flaw CVE-2026-21509 in campaigns targeting entities across Ukraine and Europe.
Who is affected?
The clearest confirmed impact is on Ukrainian military personnel and Ukrainian government environments, but the broader exposure pattern likely includes:
- defense-sector entities supporting Ukraine
- ministries and executive bodies with geopolitical relevance
- organizations interacting with Ukrainian public-sector or military workflows
- regional diplomatic, transportation, and maritime organizations already seen in adjacent APT28 activity
Where direct victim lists are unavailable, defenders should assume risk is highest where politically relevant users are exposed to phishing, malicious documents, or cloud-service-assisted post-exploitation.
Initial access & kill chain
ESET's reporting suggests a layered espionage workflow rather than a single one-shot intrusion path.
| Stage | Observed behavior | Defensive implication |
|---|---|---|
| Initial access | Malicious docs and phishing remain plausible entry routes; recent adjacent operations used Office exploitation | Block document-based delivery and isolate high-risk users |
| Execution | SlimAgent and BeardShell execute collection and PowerShell-driven actions | Watch script execution plus unusual .NET runtime behavior |
| Persistence | Modified Covenant supports stable long-term operator visibility | Hunt for recurring host identifiers and repeat beacon patterns |
| C2 | BeardShell abused Icedrive; Covenant variants used Filen, Koofr, and pCloud | Treat unusual cloud-storage traffic as possible C2, not just SaaS usage |
| Actions on objectives | Credential collection, surveillance, screenshots, clipboard theft, and operator tasking | Prioritize data exposure mapping and identity containment |
MITRE ATT&CK-aligned view
- Initial Access: Phishing / exploit delivery (reported in adjacent APT28 operations)
- Execution: PowerShell, .NET task execution
- Collection: keylogger activity, screenshots, clipboard capture
- Persistence / C2: cloud-backed C2 over legitimate services
- Discovery / Lateral Activity: operator-driven post-exploitation, potential lateral movement once footholds are established
Indicators and detection
This campaign does not hinge on a single static IOC. Defenders should focus on behavior and telemetry correlation.
What to look for
- new or rare PowerShell execution launched by unsigned or low-prevalence .NET components
- endpoints communicating with Icedrive, Filen, Koofr, or pCloud in patterns inconsistent with business use
- repeated cloud-service API traffic from high-sensitivity hosts
- HTML-formatted keystroke or surveillance logs on disk or in temp locations
- abnormal screenshot capture activity coupled with clipboard monitoring
- long-dwell remote tasking that persists after reboots or network changes
Example Splunk pattern
splindex=edr OR index=proxy | eval cloud_c2=if(match(url, "(?i)(icedrive|filen|koofr|pcloud)"), 1, 0) | stats count values(process_name) values(parent_process_name) values(dest_domain) by host user | where cloud_c2=1
Example Sentinel KQL pattern
kqlDeviceNetworkEvents | where RemoteUrl has_any ("icedrive", "filen", "koofr", "pcloud") | summarize hits=count(), processes=make_set(InitiatingProcessFileName, 10) by DeviceName, InitiatingProcessAccountName | where hits > 3
Containment & remediation checklist
🔴 Immediate containment (0-24h)
- isolate endpoints used by high-risk defense or government users showing suspicious cloud-storage beaconing
- review recent phishing and malicious document execution tied to targeted personnel
- reset credentials for users on potentially monitored hosts
- invalidate active sessions and review privileged access tokens
- preserve EDR, proxy, and PowerShell logs before cleanup
- block or tightly monitor Icedrive, Filen, Koofr, and pCloud where they are not business-critical
- perform targeted hunts for screenshot, clipboard, and keystroke collection behavior
🟠 Hardening (24-72h)
- disable or restrict Office macros and risky document handlers for exposed teams
- harden PowerShell logging, AMSI visibility, and script block capture
- segment high-value users and administrative systems from general-purpose workstations
- require MFA and conditional access for remote and cloud logins
- baseline legitimate cloud storage usage by department and geography
- review detections for renamed or modified Covenant loaders and .NET stagers
🟡 Longer-term controls (1-4 weeks)
- build threat hunts around cloud-backed C2 patterns rather than vendor-specific IOCs alone
- expand monitoring of threat intelligence on APT28 infrastructure and TTP shifts
- rehearse executive and military-user spearphishing response workflows
- implement tighter application control for scripting engines and unsigned .NET execution
- enrich detections with ATT&CK mapping and user risk context
Strategic analysis
The real trend here is not just that APT28 is active again. It is that mature state-backed operators are leaning into three durable advantages:
- Legacy code lineage with modern packaging. ESET found links between SlimAgent, XAgent, BeardShell, and older Xtunnel-era tradecraft, suggesting continuity in engineering knowledge.
- Cloud-service camouflage. By hiding C2 behind mainstream storage providers, operators gain resilience and blend with approved traffic.
- Primary and fallback implants. Covenant appears to be the main workhorse, with BeardShell retained as a secondary access path when infrastructure changes or takedowns interfere.
That combination is a strong signal for defenders in 2026: sophisticated espionage teams are optimizing for long-dwell access, operational continuity, and reduced dependence on obviously malicious infrastructure.
What happened?
APT28 was publicly linked to a renewed malware toolkit using BeardShell, SlimAgent, and a customized Covenant framework to spy on Ukrainian targets.
Who is affected?
Confirmed targeting centers on Ukrainian military personnel and government systems, with broader risk for defense, diplomatic, and adjacent regional entities.
Why is BeardShell notable?
BeardShell executes PowerShell commands and abuses Icedrive for C2, while showing code traits linked to APT28's historic toolset.
Why does Covenant matter here?
APT28 heavily modified the open-source framework for long-term espionage, including deterministic host IDs and cloud-based communications.
What should defenders do first?
Hunt for abnormal cloud-storage traffic, preserve endpoint telemetry, isolate suspicious hosts, and reset credentials for exposed users.
Is this a one-off incident?
No. Current reporting indicates sustained activity from 2024 through 2026 rather than a single short campaign.
Published: 2026-03-11 Author: Invaders Cybersecurity Classification: Public / TLP:CLEAR Reading Time: 7 minutes
References
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Threat Hunting & Intel →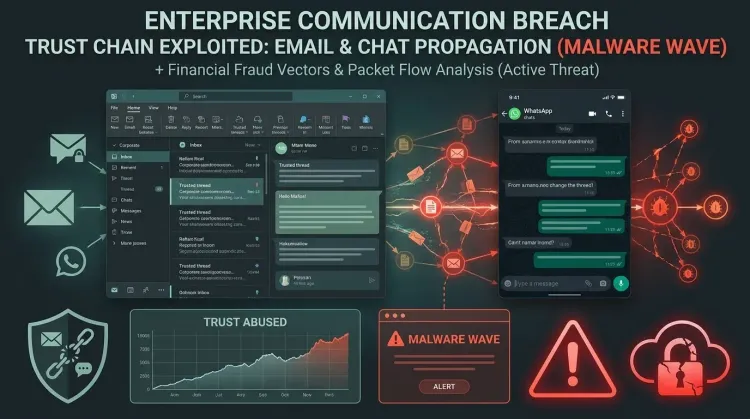 Threat Hunting & Intel
Threat Hunting & IntelTCLBANKER turns WhatsApp and Outlook into trusted malware delivery channels
TCLBANKER turns WhatsApp and Outlook into trusted malware delivery channels The most important detail in Elastic's new TCLBANKER research is not just that a Bra...
 Threat Hunting & Intel
Threat Hunting & IntelDAEMON Tools supply-chain attack turns trusted installers into a malware delivery path
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path The most important part of the DAEMON Tools incident is not that malware...
 Threat Hunting & Intel
Threat Hunting & IntelCVE-2026-41940 turns exposed cPanel and WHM servers into control-plane takeover targets
CVE-2026-41940 turns exposed cPanel and WHM servers into control-plane takeover targets CVE-2026-41940 is a critical authentication bypass in cPanel and WHM, an...