Google Warns Chrome Users to Update Now as Two Zero-Days Are Exploited
Summarize with:
Share
Google Warns Chrome Users to Update Now as Two Zero-Days Are Exploited | 2026
Executive Summary
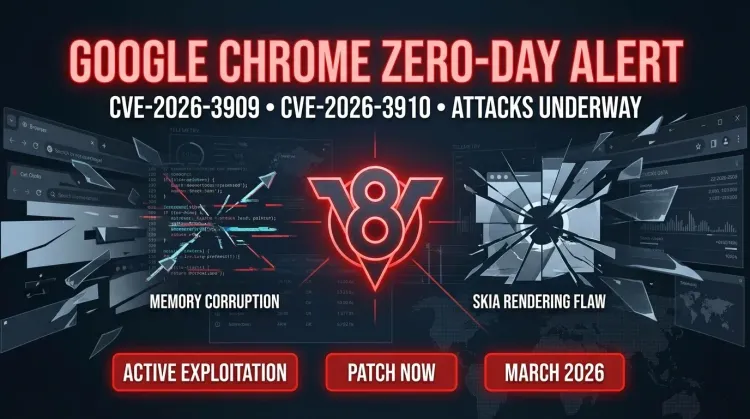
Google has pushed an emergency Chrome update after confirming that CVE-2026-3909 and CVE-2026-3910 are being exploited in the wild. The flaws affect Skia and the V8 JavaScript and WebAssembly engine, two core browser components that can turn a malicious webpage into a direct enterprise risk. For defenders, this is not a normal patch cycle issue. It is a live zero-day event with real exploitation already underway.
The headline framing around Chrome's massive user base matters, but the real operational takeaway is simpler: organizations should assume broad exposure anywhere Chrome or Chromium-based browsers are present. Browser exploitation remains one of the fastest ways to move from routine browsing into compromise attempts, especially when attackers can deliver malicious content through crafted HTML.
What happened?
Google disclosed the emergency fixes on March 12, 2026, stating that exploits exist in the wild for both vulnerabilities. One day later, CISA added both flaws to the Known Exploited Vulnerabilities (KEV) catalog, reinforcing that this is an active exploitation problem and not a hypothetical one.
Confirmed facts
- CVE-2026-3909 is an out-of-bounds write in Skia.
- CVE-2026-3910 is an inappropriate implementation vulnerability in V8.
- Google says exploits for both flaws exist in the wild.
- Fixed versions include Chrome 146.0.7680.75/76 for Windows and macOS, and 146.0.7680.75 for Linux.
- CISA added both CVEs to KEV on March 13, 2026.
- Chromium-based browsers beyond Chrome may also require attention as downstream fixes land.
What remains unclear
- Google has not disclosed attacker attribution, victimology, or exploitation chains.
- Public reporting does not yet confirm whether the two flaws are used together in one chain.
- There is no public exploit code at the time of writing.
Why this matters for defenders
1. Malicious webpages are enough to create risk
Both issues can be triggered through crafted web content. That means the attack surface is wide: ordinary browsing, phishing links, malvertising paths, and compromised websites all become relevant delivery mechanisms.
2. Chrome is only part of the exposure picture
The same upstream code base powers several Chromium-derived browsers. Even if your fleet is not standardized on Chrome alone, you still need to check whether Edge, Brave, Opera, or embedded Chromium components are lagging behind the patched versions.
3. KEV listing changes patch priority immediately
Once CISA adds a vulnerability to KEV, patching becomes an exposure-management priority rather than a best-effort maintenance task. The federal remediation timeline is specific to U.S. agencies, but the signal is useful for everyone: active exploitation is already confirmed.
Technical breakdown
CVE-2026-3909: Skia out-of-bounds write
CVE-2026-3909 affects Skia, the graphics library responsible for rendering browser content. Out-of-bounds write flaws can lead to memory corruption, crashes, and potentially code execution depending on how they are exploited.
CVE-2026-3910: V8 engine vulnerability
CVE-2026-3910 impacts V8, the JavaScript and WebAssembly engine inside Chromium. Public descriptions indicate a crafted HTML page could allow arbitrary code execution inside the browser sandbox, making it highly valuable in real-world browser exploitation.
Patch versions
Organizations should update to:
- Windows / macOS: Chrome 146.0.7680.75/76
- Linux: Chrome 146.0.7680.75
If you manage browsers through enterprise packaging or third-party vendor channels, verify when Chromium-based downstream products received the same fixes.
Timeline
| Date | Event | Status |
|---|---|---|
| 2026-03-10 | Google identified both flaws internally | ⚠️ Discovery |
| 2026-03-12 | Google released emergency desktop Chrome fixes and confirmed in-the-wild exploitation | ✅ Patch available |
| 2026-03-13 | CISA added both CVEs to KEV | 📢 KEV listing |
| 2026-03-27 | CISA remediation due date for FCEB agencies | 🔴 Patch deadline |
Detection and response guidance
Security teams should focus on speed, coverage, and validation.
Priority actions
- Inventory endpoints still running Chrome or Chromium builds below the fixed versions.
- Validate whether browser auto-update policies are working as intended.
- Hunt for suspicious browser child-process activity on systems that remained unpatched.
- Review high-risk user groups that browse untrusted content or hold privileged access.
- Confirm patch status across Chromium-based browsers beyond Chrome.
Example Splunk hunt
splindex=edr OR index=sysmon (process_name=chrome.exe OR process_name=msedge.exe OR process_name=chrome OR process_name=brave.exe) (parent_process_name=chrome.exe OR parent_process_name=msedge.exe OR parent_process_name=chrome OR parent_process_name=brave.exe) (process_name=powershell.exe OR process_name=cmd.exe OR process_name=wscript.exe OR process_name=bash) | stats count min(_time) as firstSeen max(_time) as lastSeen by host, user, parent_process_name, process_name, command_line
This is not a signature for these CVEs specifically. It is a practical hunt for suspicious child-process behavior originating from browser contexts that may justify deeper review.
Containment and remediation checklist
🔴 Immediate (0–24h)
- Push the latest Chrome stable builds to managed endpoints.
- Identify unmanaged or BYOD devices still below the patched versions.
- Notify SOC and IT operations that active browser exploitation is in scope.
- Check downstream Chromium-based browser availability and deployment status.
🟠 Near term (24–72h)
- Confirm browser restarts actually occurred so fixes are active.
- Review browser extension hygiene on privileged or high-risk devices.
- Tighten controls around browser-spawned scripting or shell activity.
- Track exceptions where legacy applications are blocking browser updates.
🟡 Longer term (1–4 weeks)
- Shorten browser patch SLAs versus general workstation updates.
- Add emergency browser patching to incident response playbooks.
- Treat KEV-listed browser flaws as a separate reporting category in vulnerability operations.
- Measure fleet update latency as a standing security metric.
Strategic analysis
This incident is a reminder that browser security still deserves the same urgency defenders give to VPNs, identity systems, and externally exposed appliances. A zero-day in a browser rendering path or JavaScript engine can scale quickly because the delivery path is familiar, low-friction, and already embedded in everyday user behavior.
The more useful framing for defenders is not the exact number of Chrome users worldwide. It is the operational reality that a massive install base, active exploitation, and delayed restart behavior combine into a very large patching window for attackers to target.
What are CVE-2026-3909 and CVE-2026-3910?
They are two high-severity Chrome zero-days affecting the Skia graphics library and the V8 JavaScript/WebAssembly engine. Google says both have been exploited in the wild.
Why should enterprises care immediately?
Because Google confirmed active exploitation and CISA added both flaws to KEV. That makes patch timing materially important.
Are only Chrome users affected?
Not necessarily. Other Chromium-based browsers and products may also need the same upstream fixes.
What should teams do first?
Patch Chrome immediately, verify downstream Chromium exposure, and hunt for suspicious browser-driven execution on systems that lagged updates.
Is there public exploit code?
Not at the time of writing. Google has restricted technical details while patches roll out.
References
- Google Chrome Releases - Stable Channel Update for Desktop
- CISA Adds Two Known Exploited Vulnerabilities to Catalog
- Google fixes two new Chrome zero-days exploited in attacks
- Google Fixes Two Chrome Zero-Days Exploited in the Wild Affecting Skia and V8
- Google rushes Chrome update fixing two zero-days already under attack
Published: 2026-03-15 Author: Invaders Cybersecurity Classification: Public / TLP:CLEAR Reading Time: 5 minutes
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in vulnerability →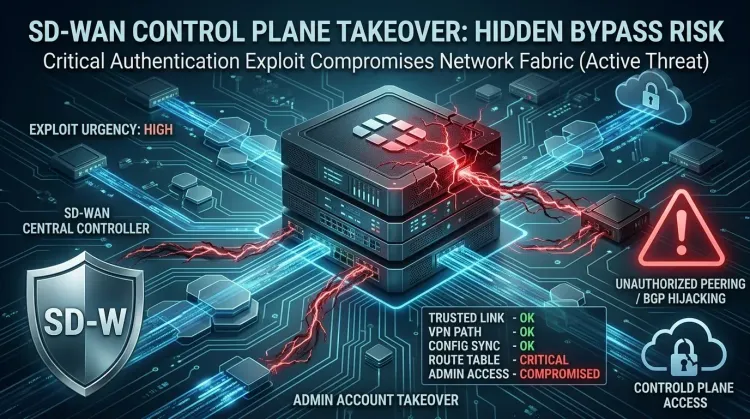 vulnerability
vulnerabilityCVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority
CVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority CVE-2026-20182 is not landing as a routine patch bulletin. Cisco says the flaw is already b...
 vulnerability
vulnerabilityExim BDAT flaw makes mail servers urgent RCE patch targets
Exim BDAT flaw makes mail servers urgent RCE patch targets CVE-2026-45185 is the kind of bug that forces defenders to remember an old lesson: email infrastructu...
 vulnerability
vulnerabilityDirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag is the kind of Linux bug defenders worry about because it turns a limited foot...