Cisco SD-WAN Flaws CVE-2026-20122 and CVE-2026-20128 Face Active Exploitation
Summarize with:
Share
Cisco SD-WAN Flaws CVE-2026-20122 and CVE-2026-20128 Face Active Exploitation | 2026
Executive Summary
CVE-2026-20122 and CVE-2026-20128 have turned Cisco's SD-WAN exposure story into a broader management-plane security problem. Cisco says both vulnerabilities in Catalyst SD-WAN Manager are now being actively exploited, extending the urgency created by the earlier zero-day around CVE-2026-20127.
For defenders, the key takeaway is that this is no longer just a single bug or a routine maintenance issue. Organizations running internet-exposed SD-WAN management systems should assume attackers are probing for any weakness that can help them move from initial access into privilege abuse, credential exposure, or deeper lateral movement inside the network.
What are CVE-2026-20122 and CVE-2026-20128?
CVE-2026-20122 is a high-severity arbitrary file overwrite flaw in the API of Cisco Catalyst SD-WAN Manager. According to Cisco, an attacker with valid read-only credentials and API access can upload a malicious file, overwrite local files, and gain vmanage user privileges.
CVE-2026-20128 is a medium-severity information disclosure issue in the Data Collection Agent feature. A low-privileged local user with valid vmanage credentials can retrieve a stored DCA password and use it to gain DCA user privileges on another affected system.
Cisco's March advisory update says that CVE-2026-20122 and CVE-2026-20128 are the two issues from this advisory that are known to be under active exploitation. That matters because it shows attackers are not just chasing headline-grabbing unauthenticated bugs. They are also exploiting post-auth and credential-adjacent weaknesses when those paths help preserve access.
Why this matters now
1. SD-WAN management planes are high-value targets
A compromised SD-WAN management layer gives attackers visibility into network topology, policy, and device relationships. In practical terms, that makes these platforms strategic infrastructure rather than ordinary admin panels.
2. Exploitation is expanding beyond the original zero-day narrative
Cisco Talos linked earlier SD-WAN exploitation to a sophisticated actor tracked as UAT-8616, which targeted Cisco SD-WAN environments as far back as 2023. The new exploitation status for CVE-2026-20122 and CVE-2026-20128 suggests defenders should broaden hunting and remediation beyond the original zero-day focus on CVE-2026-20127.
3. Credential exposure can become operational access
The risk here is not just disclosure in the abstract. Exposed service credentials, overwritten files, and abuse of internal trust relationships can become stepping stones to persistence, policy manipulation, or expanded access across the SD-WAN environment.
Technical breakdown
CVE-2026-20122: arbitrary file overwrite in the API
Cisco describes CVE-2026-20122 as an improper file handling issue in the API of Catalyst SD-WAN Manager. An attacker needs valid read-only credentials with API access, but once inside that boundary they may be able to overwrite arbitrary files and elevate to vmanage privileges.
That makes this flaw especially dangerous in environments where credential hygiene is weak or where operational accounts are shared across teams and systems.
CVE-2026-20128: information disclosure via the DCA feature
CVE-2026-20128 stems from the presence of a DCA credential file on affected systems. A low-privileged user who can access the file system may extract the stored password and pivot into DCA access on another affected system.
In other words, this is the kind of information disclosure bug that can still have meaningful operational impact when paired with real access and weak internal segmentation.
Timeline
| Date | Event | Status |
|---|---|---|
| 2026-02-25 | Cisco publishes advisory covering multiple Catalyst SD-WAN Manager flaws | 📢 Public disclosure |
| 2026-02-25 | Cisco Talos discloses active exploitation tied to CVE-2026-20127 and UAT-8616 activity dating back to 2023 | 🔴 Active exploitation |
| 2026-02-28 | CISA issues Emergency Directive 26-03 for Cisco SD-WAN systems after exploitation concerns | ⚠️ Emergency action |
| 2026-03-05 | Cisco update says CVE-2026-20122 and CVE-2026-20128 are also under active exploitation | 🔴 Active exploitation |
| 2026-03-16 | Defenders continue patching and validating exposure across SD-WAN estates | 🔍 Ongoing response |
Detection and response guidance
Priority actions
- Identify every instance of Catalyst SD-WAN Manager exposed to untrusted networks.
- Patch to Cisco's fixed software releases without waiting for the next maintenance cycle.
- Review API and
vmanageaccounts for unnecessary access, stale credentials, and shared usage. - Inspect systems for suspicious file changes, unauthorized accounts, and unexplained peer relationships.
- Expand incident response scoping to include related controllers, managers, and connected edge devices.
What to hunt for
Cisco Talos recommends focusing first on unexpected control-connection peering events in SD-WAN logs, particularly those involving unusual public IPs, unexpected peer types, or timings that do not match maintenance windows. Defenders should also review:
- unexplained or unauthorized SSH keys
- evidence of root sessions on production systems
- abnormally small or truncated logs
- suspicious version downgrades or upgrades followed by reboot activity
- signs that attackers attempted to hide activity after initial access
Example Splunk hunt
splindex=network OR index=syslog ("VDAEMON_0" OR "control-connection-state-change") (peer-type=vmanage OR peer-type=vsmart OR peer-type=vbond OR peer-type=vedge) | stats count min(_time) as firstSeen max(_time) as lastSeen by host, public_ip, peer_system_ip, peer_type | sort - lastSeen
This is not a signature for a single exploit chain. It is a practical hunt for suspicious SD-WAN peering activity that deserves validation by network and security teams.
Mitigation checklist
🔴 Immediate
- Apply Cisco's fixed releases for all affected SD-WAN Manager versions.
- Restrict management-plane exposure to trusted administrative networks.
- Rotate credentials for privileged and service accounts associated with SD-WAN operations.
- Review whether any read-only API credentials are broader than they need to be.
🟠 Near term
- Validate that patches are active and that services were restarted where needed.
- Compare current software versions against Cisco's advisory guidance.
- Review segmentation around SD-WAN management components and supporting services.
- Check for anomalous administrator activity since late February.
🟡 Strategic
- Treat network-edge platforms as priority assets in threat intelligence and exposure-management programs.
- Shorten patch SLAs for management-plane and edge infrastructure.
- Add SD-WAN log review and hardening checks to standing operational playbooks.
Bottom line
Cisco's SD-WAN incident is widening from a single exploited bug into a cluster of management-plane weaknesses that attackers can abuse in sequence.
Key takeaways
✅ Patch now — Cisco says CVE-2026-20122 and CVE-2026-20128 are already being exploited.
✅ Scope wider than one CVE — environments checked only for CVE-2026-20127 may still miss active risk.
✅ Hunt for trust abuse — credential exposure, file overwrite, and suspicious peering events are all meaningful signals.
If your organization runs Cisco Catalyst SD-WAN Manager, treat this as an active compromise-risk event and verify exposure, patch status, and post-exploitation artifacts immediately.
Are CVE-2026-20122 and CVE-2026-20128 unauthenticated remote bugs?
Not exactly. Cisco says CVE-2026-20122 requires valid read-only credentials with API access, and CVE-2026-20128 requires valid low-privileged local access with vmanage credentials. Even so, both are being actively exploited.
Why is this still urgent if credentials are required?
Because real environments often have over-privileged service accounts, reused credentials, and exposed management interfaces. Once attackers get a foothold, these flaws can help them deepen access.
Is this the same issue as CVE-2026-20127?
No. CVE-2026-20127 was the earlier critical authentication bypass tied to zero-day exploitation. Cisco now says CVE-2026-20122 and CVE-2026-20128 are also under active attack.
References
- Cisco Security Advisory: Multiple Vulnerabilities in Cisco Catalyst SD-WAN Manager
- Cisco Talos: Active exploitation of Cisco Catalyst SD-WAN by UAT-8616
- CISA Emergency Directive 26-03: Mitigate Vulnerabilities in Cisco SD-WAN Systems
- BleepingComputer: Cisco flags more SD-WAN flaws as actively exploited in attacks
- The Hacker News: Cisco Confirms Active Exploitation of Two Catalyst SD-WAN Manager Vulnerabilities
Published: 2026-03-16 Author: Invaders Cybersecurity Classification: Public / TLP:CLEAR Reading Time: 5 minutes
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in vulnerability →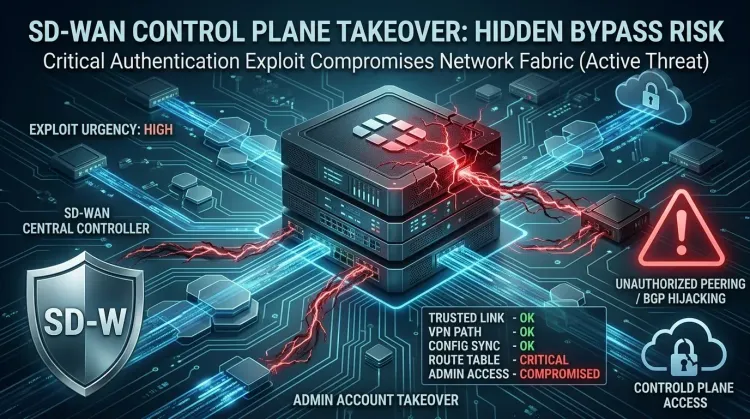 vulnerability
vulnerabilityCVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority
CVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority CVE-2026-20182 is not landing as a routine patch bulletin. Cisco says the flaw is already b...
 vulnerability
vulnerabilityExim BDAT flaw makes mail servers urgent RCE patch targets
Exim BDAT flaw makes mail servers urgent RCE patch targets CVE-2026-45185 is the kind of bug that forces defenders to remember an old lesson: email infrastructu...
 vulnerability
vulnerabilityDirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag is the kind of Linux bug defenders worry about because it turns a limited foot...