Axios npm compromise pushed a cross-platform RAT through a fake dependency
Summarize with:

Share
Axios npm compromise pushed a cross-platform RAT through a fake dependency
A compromise of the widely used axios package on npm shows why defenders cannot rely only on source diffs or release notes when evaluating package risk. In the malicious releases, attackers did not visibly backdoor Axios source code. Instead, they introduced a hidden dependency, [email protected], whose postinstall hook executed automatically during installation and fetched platform-specific malware.
That distinction matters. This was not just a software supply chain story about a poisoned package version. It was a trusted publication-path failure that could turn routine package installation on developer workstations, CI runners, and build hosts into remote code execution and credential exposure.
What happened in the Axios compromise
Public reporting from Socket says the malicious npm releases included [email protected] and [email protected]. Those versions pulled in [email protected], which Socket identified as malicious.
According to the reporting reviewed for this post, the attacker kept the Axios-side change minimal: just enough to add the dependency and let npm do the rest. That is a familiar pattern in supply chain attacks, because transitive dependencies often receive less scrutiny than headline package code.
The release behavior also appeared suspicious from a governance perspective. The affected version reportedly did not line up with the project’s normal GitHub tagging pattern, and public discussion suggested maintainers were still working to regain control of the release path and revoke risky publication access.
Why the hidden dependency was so dangerous
The malicious package did not wait for the application to run. It used the npm postinstall lifecycle event, meaning the attack chain could begin as soon as a system installed the dependency tree.
Researchers say the dropper used obfuscation, then branched into platform-specific payload delivery for Windows, macOS, and Linux. Reported behaviors included:
- downloading follow-on payloads from attacker infrastructure
- launching platform-native execution chains such as
osascript,powershell,cscript,curl, orpython3 - attempting anti-forensics cleanup after execution
- replacing or deleting package files to hide the malicious install-time logic
That last point is especially important for incident response. A compromised dependency that erases the obvious signs of its own presence can leave teams with a false sense of safety if they only inspect node_modules after the fact.
Cross-platform malware impact is the real story
Several researchers described the second-stage outcome as a remote access trojan or RAT with cross-platform delivery paths. Socket’s analysis described staged malware capable of arbitrary command execution, system-data collection, and persistence-oriented behavior. Elastic’s write-up also focused on the broader shared RAT architecture across operating systems.
For defenders, the practical lesson is straightforward: if one of the affected versions was installed, do not frame the problem as “we pulled a bad dependency.” Frame it as a host-compromise event with potential downstream credential theft, malware execution, and lateral follow-on risk.
That is especially true for systems with privileged environment data, including:
- developer workstations with cloud CLIs, SSH keys, and local secrets
- CI runners with tokens, signing material, or deployment credentials
- build servers that can reach registries, internal repositories, or production-adjacent infrastructure
Affected versions and what to look for
Current reporting consistently points to these versions as the key exposure set:
The attacker infrastructure and indicators highlighted in reporting included the domain sfrclak[.]com, associated network activity to 142.11.206.73, and suspicious install-time process chains involving shell interpreters, scripting engines, or download tools.
Teams should review:
- lockfiles and dependency snapshots
- feature branches and open pull requests
- CI/CD job logs around package installation
- endpoint telemetry for suspicious install-time child processes
- outbound connections made during npm install workflows
Why rollback alone is not enough
With package incidents, teams often default to “remove the bad version and reinstall.” That response is too shallow here.
If the malicious package already executed, the relevant question is not only whether the dependency remains present. The real question is what the malware did while it had execution. That can include secret theft, payload staging, process execution, and persistence attempts.
A safer response pattern is:
🔴 Identify and isolate impacted hosts
- Find systems that installed or executed the affected Axios versions.
- Prioritize developer endpoints, shared CI runners, and any host with privileged build or deployment access.
🔴 Rotate secrets from a clean machine
- Treat accessible API keys, tokens, SSH material, registry credentials, and cloud credentials as potentially exposed.
- Rotate from known-clean infrastructure, not from the possibly impacted host.
🔴 Hunt for malware behaviors, not just package names
- Review process trees spawned during install events.
- Investigate suspicious uses of
curl,python3,osascript,powershell, orcscripttied to package installation. - Check network logs for connections to known attacker-controlled infrastructure.
🟠 Review downstream trust paths
- Determine whether the host could access signing workflows, internal package registries, production deployment paths, or source control secrets.
- If yes, extend the review beyond the single machine and into the broader attack surface.
Strategic takeaway
The Axios incident is a sharp reminder that defenders cannot evaluate package safety only by reading the top-level repository diff. A single dependency change in a trusted release can be enough to deliver cross-platform malware at install time.
For security teams, the priority is to think in layers: package version review, lockfile hygiene, trusted publishing, provenance checks, install-time telemetry, and strong control over maintainer publication paths. And when a compromise like this lands, the right mindset is simple: if the affected package was installed, assume host risk first and dependency cleanup second.
References
- Supply Chain Attack on Axios Pulls Malicious Dependency from npm
- Axios issue discussing the compromise
- GitHub Advisory Database entry
- Axios compromised on npm: malicious versions drop remote access trojan
- Axios: One RAT to rule them all
- Axios npm compromised in supply chain attack
- Axios npm package compromised: supply chain attack delivers cross-platform RAT
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Supply Chain Security →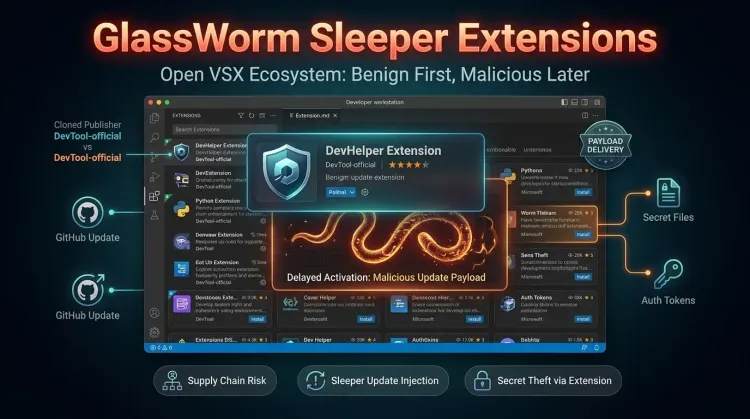 Supply Chain Security
Supply Chain SecurityGlassWorm sleeper extensions turn Open VSX updates into a malware delivery path
GlassWorm sleeper extensions turn Open VSX updates into a malware delivery path The newest GlassWorm wave matters because it turns the normal extension update p...
 Supply Chain Security
Supply Chain SecurityBitwarden CLI npm compromise exposes CI/CD credential risk
Bitwarden CLI npm compromise exposes CI/CD credential risk A brief compromise of the Bitwarden CLI npm distribution is still a high-priority defender story beca...
 Supply Chain Security
Supply Chain SecurityCisco Breach Shows the Real Cost of the Trivy Supply-Chain Attack
Cisco Breach Shows the Real Cost of the Trivy Supply-Chain Attack The most important lesson from the Trivy incident is that a supply-chain attack on a trusted s...