Microsoft March 2026 Patch Tuesday Fixes Two Zero-Days
Summarize with:
Share
Why This Patch Tuesday Matters
Microsoft's March 2026 Patch Tuesday addressed 79 vulnerabilities, including two publicly disclosed zero-days and three critical remote code execution flaws. While none were confirmed actively exploited at release, the combination of Office preview-pane RCE and SQL Server privilege escalation makes this cycle particularly high-stakes for enterprise defenders.
Zero-Days and Critical CVEs
| CVE | Component | CVSS | Type | Priority |
|---|---|---|---|---|
| CVE-2026-26107 | SQL Server | 8.8 | Privilege Escalation | Critical — patch now |
| CVE-2026-26082 | .NET Framework | 7.5 | Denial of Service | High |
| CVE-2026-26110 | Microsoft Office | 8.0 | RCE via Preview Pane | Critical — patch now |
| CVE-2026-26113 | Microsoft Office | 7.8 | RCE via Preview Pane | Critical — patch now |
| CVE-2026-26144 | Microsoft Excel | 6.5 | Information Disclosure | Medium |
CVE-2026-26107: An authorized attacker can escalate to SQLAdmin over the network without physical access. If SQL Server is reachable from a compromised endpoint, this is lateral movement made trivial.
Priority Areas for Defenders
1. Office Preview-Pane RCE
Preview-pane exploitation lowers the bar significantly — a user doesn't need to open the file. Prioritize Office patches for finance, HR, legal, and executive support teams who receive external attachments daily.
Compensating controls while patch validation runs:
- Enable attachment sandboxing / CDR (content disarm and reconstruct)
- Block macro-capable file types at the email gateway
- Monitor Office process spawning child processes
2. SQL Server Privilege Escalation
Elevating to SQLAdmin from an authorized low-privilege account is a bridge to broader compromise: data exfiltration, persistence via SQL Agent jobs, and lateral movement into connected systems.
Immediate actions:
- Audit which accounts have SQL Server access and from where
- Enable SQL Server audit logging if not already active
- Restrict SQL Server port (1433) to known application servers only
3. Excel Copilot Data Egress
CVE-2026-26144 is a reminder that AI-assisted workflows are now inside the attack surface. If Copilot can move data across trust zones, validate outbound policies from workstations handling sensitive spreadsheets.
Recommended Response Steps
- Patch Office and SQL Server endpoints first — highest attacker interest, broad enterprise exposure
- Review email attachment controls — preview-pane RCE makes attachment handling a first-line control
- Audit SQL privilege paths — identify where low-privilege accounts can escalate
- Check Copilot/AI egress boundaries — review outbound connections from Office-enabled systems
Conclusion
March 2026 Patch Tuesday reflects a pattern: traditional vulnerabilities now intersect with AI tooling, cloud-connected administration, and deeply embedded business workflows. Remediation requires understanding how a single flaw might influence identity, data flow, and endpoint trust simultaneously.
Sources
- BleepingComputer — Microsoft March 2026 Patch Tuesday — March 10, 2026
- Microsoft MSRC — March 2026 Security Updates — Microsoft Security Response Center
FAQ
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in Security →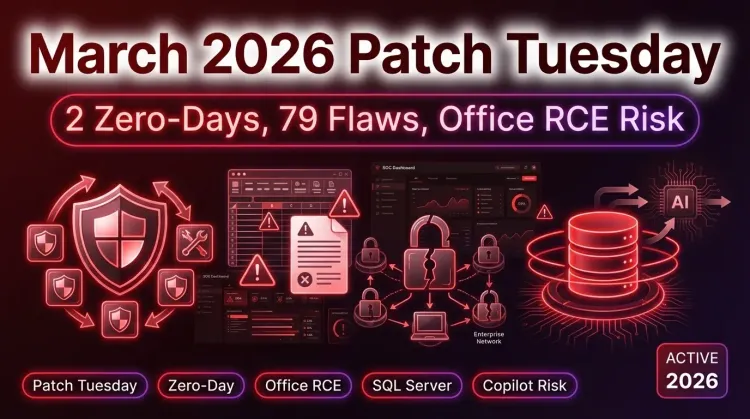 Security
SecurityMicrosoft March 2026 Patch Tuesday Fixes Two Publicly Disclosed Zero-Days and 79 Vulnerabilities
Microsoft March 2026 Patch Tuesday Fixes Two Publicly Disclosed Zero-Days and 79 Vulnerabilities Microsoft’s March 2026 Patch Tuesday landed with a broad securi...
 Security
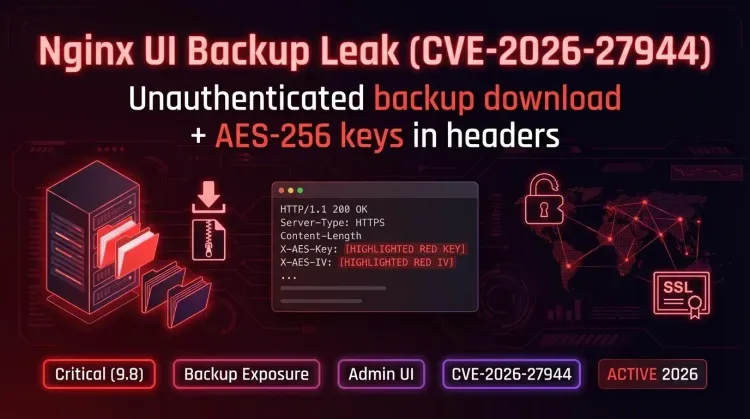
SecurityCritical Nginx UI Flaw (CVE-2026-27944) Exposes Server Backups
Critical Nginx UI Flaw (CVE-2026-27944) A critical vulnerability has been reported in Nginx UI, tracked as CVE-2026-27944 (CVSS 9.8). The flaw allows unauthenti...