CVE-2026-5194 weakens wolfSSL certificate trust in embedded deployments
Summarize with:

Share
CVE-2026-5194 weakens wolfSSL certificate trust in embedded deployments
CVE-2026-5194 is a reminder that core cryptographic libraries can create outsized enterprise risk even when the bug is buried inside a lightweight component. In vulnerable wolfSSL builds, missing checks around digest size and object identifiers during signature verification can let affected systems accept certificate signatures that should fail. That turns a low-level vulnerability in a trusted library into a real trust-boundary problem.
The risk matters because wolfSSL is widely used in embedded products, industrial systems, appliances, routers, automotive environments, and other deployments where patch cycles can move slowly. If a device or application makes the wrong trust decision during certificate validation, defenders may end up with a broken encryption path without obvious operational symptoms.
What the flaw changes
According to the GitHub advisory and NVD entry, wolfSSL failed to fully enforce digest-size and OID checks when verifying certain signatures. In practical terms, that means a crafted certificate can be validated with a digest smaller than what the algorithm and key type should permit.
The issue affects ECDSA/ECC verification when EdDSA or ML-DSA is also enabled. The advisory warns that this can reduce the security of certificate-based authentication, especially if the relevant public certificate authority key is known.
This is not the kind of bug defenders should dismiss as purely academic. Certificate validation is one of the control points that decides whether a system trusts a remote endpoint, service, or signed object. Weakening that verification path can create room for forged identities or downgraded trust assumptions.
Why defenders should care
The operational story is not just about one library release. It is about dependency reach.
wolfSSL is built into many environments where defenders do not patch the library directly. Instead, they depend on firmware vendors, appliance makers, SDK maintainers, or Linux distribution packaging. That means exposure can persist even after a fix exists upstream.
For security teams, the immediate concern is not mass exploitation headlines. It is the quiet possibility that vulnerable devices or applications continue to make unsafe trust decisions long after the upstream patch ships. In embedded and OT-adjacent environments, that kind of delay can be more dangerous than a noisy one-click exploit, because it hides inside normal secure-channel assumptions.
Patch and exposure details
Public reporting says the flaw was addressed in wolfSSL 5.9.1, released on 2026-04-08. NVD maps the issue to CWE-295: Improper Certificate Validation and shows a CVSS 4.0 vector from wolfSSL indicating high confidentiality and integrity impact.
Defenders should not stop at version checks on directly managed systems. They should also ask:
- which products in the environment embed wolfSSL rather than link it visibly
- which vendors have published downstream advisories or firmware updates
- whether any certificate-validation-heavy workflows rely on affected builds in exposed or sensitive segments
What to do now
1. Identify direct and indirect wolfSSL usage
Inventory products, SDKs, firmware images, and appliances that embed wolfSSL. This is especially important in edge devices, industrial gateways, custom embedded applications, and products with long lifecycle support windows.
2. Prioritize updates to wolfSSL 5.9.1 or vendor-fixed builds
If you manage the library directly, update immediately. If wolfSSL is bundled inside a third-party product, track the vendor advisory and patch timeline rather than assuming the upstream release solved your exposure.
3. Review certificate-dependent trust paths
Look closely at systems that authenticate peers or services through client certificates, internal PKI, device-to-device trust, or signed update channels. Anywhere certificate validation is a security boundary deserves review.
4. Segment and monitor sensitive embedded estates
Where patching will lag, tighten access control around management interfaces and reduce unnecessary network reachability. For high-value environments, increase monitoring around unusual TLS failures, certificate anomalies, and unexpected trust relationships.
Strategic takeaway
CVE-2026-5194 shows why defenders need software composition visibility beyond mainstream enterprise packages. A flaw in a compact TLS library can ripple into embedded fleets, OEM products, and operational technology environments where security teams may not even realize the dependency exists.
The right response is not only to patch wolfSSL. It is to treat certificate validation issues as infrastructure trust problems, then verify where that trust is inherited across devices, software supply chains, and vendor-managed platforms.
What is CVE-2026-5194?
CVE-2026-5194 is a certificate-validation flaw in wolfSSL caused by missing digest-size and OID checks during signature verification.
What is the main security impact?
Affected systems may accept signatures or certificates that should be rejected, weakening certificate-based authentication and trust decisions.
Which environments are most exposed?
Environments using wolfSSL in embedded products, IoT devices, appliances, industrial systems, or vendor-bundled software are the most important to review, especially where patching depends on third parties.
What is the fix?
The upstream fix is in wolfSSL 5.9.1. Downstream users should also look for vendor-specific firmware or package updates.
References
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in vulnerability →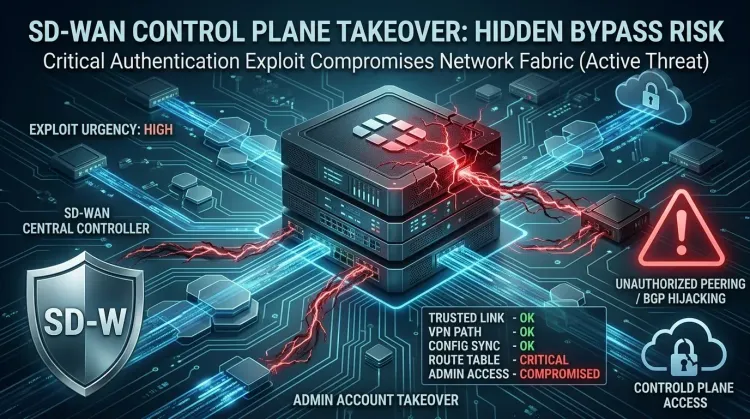 vulnerability
vulnerabilityCVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority
CVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority CVE-2026-20182 is not landing as a routine patch bulletin. Cisco says the flaw is already b...
 vulnerability
vulnerabilityExim BDAT flaw makes mail servers urgent RCE patch targets
Exim BDAT flaw makes mail servers urgent RCE patch targets CVE-2026-45185 is the kind of bug that forces defenders to remember an old lesson: email infrastructu...
 vulnerability
vulnerabilityDirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag is the kind of Linux bug defenders worry about because it turns a limited foot...