Cisco warns of actively exploited Catalyst SD-WAN Manager flaws (CVE-2026-20122, CVE-2026-20128)
Summarize with:
Share
Cisco flags more SD-WAN flaws as actively exploited in attacks
Cisco updated an advisory to confirm active exploitation of two vulnerabilities affecting Catalyst SD-WAN Manager (formerly vManage), the centralized management plane used to administer large SD-WAN deployments. When a management plane is compromised, attackers can often pivot into the wider network and persist.
What happened (high level)
Cisco says it has observed active exploitation of:
- CVE-2026-20122 — High severity, arbitrary file overwrite; remote exploitation requires valid read-only credentials with API access.
- CVE-2026-20128 — Medium severity, information disclosure; requires valid vManage credentials on the target.
Cisco also notes these issues impact Catalyst SD-WAN Manager regardless of configuration and recommends upgrading to fixed releases.
Why it matters
Even when exploitation requires credentials, real-world compromise paths are common: credential reuse, stolen VPN creds, infostealers, leaked API keys, or low-privilege access from another foothold.
For organizations running SD-WAN at scale, the management plane is a high-value target because it can:
- change routing/policies,
- deploy configuration to many edges,
- create new peers, and
- enable broad visibility (and therefore broad data exposure) if compromised.
What to do now (practical checklist)
- Inventory Catalyst SD-WAN Manager/vManage instances (including DR/standby).
- Patch/upgrade to Cisco fixed releases as advised.
- Audit accounts with SD-WAN API access (especially read-only accounts that may still have API permissions).
- Rotate credentials associated with SD-WAN admin/API users; enforce MFA where supported.
- Review logs for unusual API activity (bulk reads, config export, unexpected file operations) around the advisory window.
- If you suspect compromise, follow an incident playbook: isolate management plane, capture artifacts, and validate controller/edge integrity.
Source
BleepingComputer — Cisco flags more SD-WAN flaws as actively exploited in attacks (March 2026): https://www.bleepingcomputer.com/news/security/cisco-flags-more-sd-wan-flaws-as-actively-exploited-in-attacks/
Note: This post is a summary for security teams. Always follow the vendor advisory for the authoritative upgrade matrix.
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in vulnerability →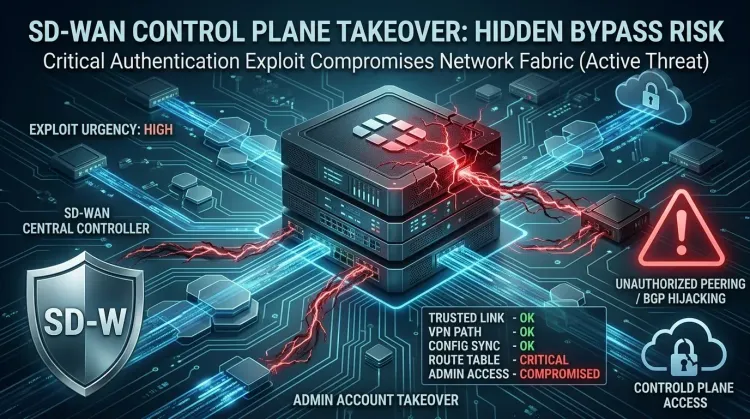 vulnerability
vulnerabilityCVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority
CVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority CVE-2026-20182 is not landing as a routine patch bulletin. Cisco says the flaw is already b...
 vulnerability
vulnerabilityExim BDAT flaw makes mail servers urgent RCE patch targets
Exim BDAT flaw makes mail servers urgent RCE patch targets CVE-2026-45185 is the kind of bug that forces defenders to remember an old lesson: email infrastructu...
 vulnerability
vulnerabilityDirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag is the kind of Linux bug defenders worry about because it turns a limited foot...