Apache ActiveMQ RCE CVE-2026-34197 Lands in CISA KEV
Summarize with:
Share
Apache ActiveMQ RCE CVE-2026-34197 lands in CISA KEV
Executive summary
CISA has added CVE-2026-34197 to the Known Exploited Vulnerabilities catalog after attackers began exploiting a high-severity flaw in Apache ActiveMQ Classic. The issue affects brokers before 5.19.4 and 6.2.3 and can let an authenticated attacker achieve remote code execution through the web console’s Jolokia JMX-HTTP bridge. For defenders, the practical takeaway is simple: if ActiveMQ web consoles are reachable and administrative access is exposed, this moves from a patching task to an urgent exposure review and incident response problem.
What happened?
According to Apache’s advisory, the flaw sits in how ActiveMQ Classic handles certain operations exposed through the Jolokia endpoint on the web console. The default policy permits exec operations on ActiveMQ MBeans, including methods that can add connectors. A crafted discovery URI can abuse the brokerConfig parameter to load a remote Spring XML application context before validation fully completes, leading to arbitrary code execution on the broker JVM.
The timeline matters:
- April 7, 2026: the CVE was published with vendor guidance to upgrade.
- April 16, 2026: CISA added the flaw to KEV, confirming active exploitation in the wild.
- Current defender implication: exposed or weakly controlled ActiveMQ admin surfaces should be treated as high priority because ActiveMQ has already been a repeat target for ransomware operators and opportunistic post-exploitation.
Why this flaw matters beyond the CVSS label
This is not just another message broker patch notice. ActiveMQ often sits in environments where it connects business applications, middleware, integration pipelines, and internal services. That means a successful compromise can give an attacker more than code execution on one server. It can become a foothold for lateral movement, credential theft, or follow-on disruption inside a trusted application zone.
The attack path is also operationally realistic. The bug requires authentication, but that does not reduce the urgency if:
- the admin console is internet-exposed
- credentials are weak, reused, or already compromised
- an attacker already has low-level internal access
- monitoring on management APIs is limited
In real environments, authenticated flaws often become “easy mode” once perimeter mistakes or stolen credentials are in play.
Affected versions
Apache says the vulnerability affects:
- Apache ActiveMQ Broker / ActiveMQ Classic before 5.19.4
- Apache ActiveMQ Broker / ActiveMQ Classic 6.0.0 through 6.2.2
- packages such as
activemq-allin the same vulnerable version ranges
The recommended fix is to upgrade to 5.19.4 or 6.2.3.
What defenders should check right now
1. Find exposed ActiveMQ consoles
Identify any internet-facing or broadly reachable ActiveMQ web consoles, especially those exposing Jolokia under paths such as /api/jolokia/. If the console is reachable from untrusted networks, reduce access immediately.
2. Review administrative access control
Check who can authenticate to ActiveMQ management interfaces. Review local admin accounts, shared credentials, legacy service accounts, and any reverse proxies or SSO layers in front of the console.
3. Hunt for exploitation clues
Public reporting highlights suspicious broker connections using a brokerConfig=xbean:http:// style parameter together with internal VM transport behavior. Review broker logs, web console access logs, reverse proxy telemetry, and process execution records for signs that the broker loaded unexpected remote Spring XML content.
4. Look for post-exploitation
Because the flaw enables arbitrary code execution, follow the patch with a short compromise assessment. Hunt for suspicious child processes, download-and-execute behavior, unusual network egress, persistence artifacts, and any new command-and-control channels from the broker host.
Detection and triage ideas
Log and proxy review
- Requests to Jolokia endpoints from unusual external IPs
- Access to management paths outside normal admin hours
- Parameters containing
brokerConfig=or unusualxbean:URIs - Sudden creation of new connectors or network connectors in broker logs
Endpoint / server telemetry
- Java processes spawning shells, script interpreters, or package managers
- Outbound network connections from the broker host to unexpected external infrastructure
- New cron jobs, startup entries, or systemd units after suspected exploitation
- Unexpected archive downloads or staging activity from the ActiveMQ server
Prioritization guidance
Patch internet-facing brokers first, then any broker reachable from shared internal segments, jump hosts, developer enclaves, or third-party connected environments.
Recommended response plan
Immediate, today
- Upgrade vulnerable ActiveMQ instances to 5.19.4 or 6.2.3
- Restrict access to the web console and Jolokia endpoint
- Rotate administrative credentials if exposure is plausible
- Review logs for exploitation attempts since the patch window opened
Next 24 to 72 hours
- Validate that no unnecessary management interfaces remain reachable
- Add focused detections for
brokerConfigabuse and suspicious Java child process execution - Review segmentation around brokers that connect high-value apps or data flows
- Document where ActiveMQ is still business-critical and where it can be isolated further
Strategic take
CISA’s KEV decision is the real signal here. It means defenders should stop treating this as a routine middleware upgrade and start treating it as an actively used intrusion path. ActiveMQ is not obscure infrastructure, and messaging middleware often sits in places that are trusted by design. When an authenticated management flaw reaches KEV, organizations need to answer two questions fast: are we exposed, and do we have evidence someone touched it?
That is the right angle for today’s response. Patch, reduce management-plane exposure, and perform a lightweight compromise assessment instead of assuming the upgrade alone closes the risk.
What is CVE-2026-34197?
It is an Apache ActiveMQ Classic vulnerability that can let an authenticated attacker achieve remote code execution through the Jolokia-backed management path.
Is this being exploited?
Yes. CISA added it to KEV on April 16, 2026, which means exploitation has been observed in the wild.
Does authentication make it low risk?
No. Authenticated flaws still matter when admin consoles are exposed, credentials are weak or stolen, or attackers already have an internal foothold.
What should teams do first?
Upgrade, limit access to the console, review logs for exploitation patterns, and check for post-exploitation activity on the broker host.
References
Written by
Lucas Oliveira
Research
A DevOps engineer and cybersecurity enthusiast with a passion for uncovering the latest in zero-day exploits, automation, and emerging tech. I write to share real-world insights from the trenches of IT and security, aiming to make complex topics more accessible and actionable. Whether I’m building tools, tracking threat actors, or experimenting with AI workflows, I’m always exploring new ways to stay one step ahead in today’s fast-moving digital landscape.
Get the latest cybersecurity insights in your inbox.
You Might Also Like
More in vulnerability →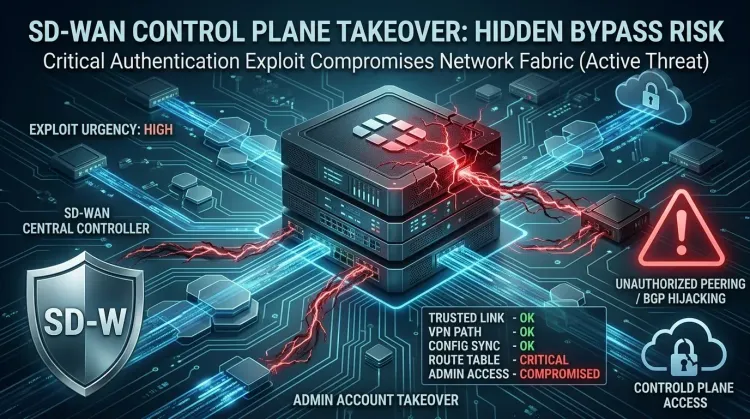 vulnerability
vulnerabilityCVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority
CVE-2026-20182 makes Cisco SD-WAN controllers an urgent KEV priority CVE-2026-20182 is not landing as a routine patch bulletin. Cisco says the flaw is already b...
 vulnerability
vulnerabilityExim BDAT flaw makes mail servers urgent RCE patch targets
Exim BDAT flaw makes mail servers urgent RCE patch targets CVE-2026-45185 is the kind of bug that forces defenders to remember an old lesson: email infrastructu...
 vulnerability
vulnerabilityDirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag is the kind of Linux bug defenders worry about because it turns a limited foot...